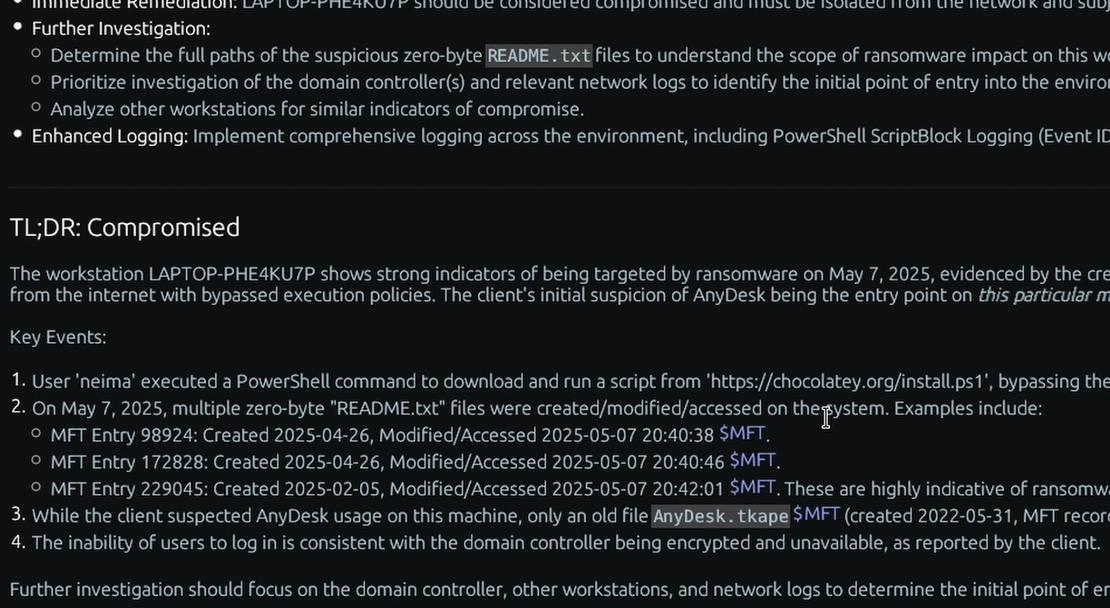
What is the “USN Journal” Windows forensic artifact?
The Update Sequence Number (USN) Journal is a critical, hidden system file within the New Technology File System (NTFS) designed to log changes made to files and directories on a volume. Located within the $Extend\$UsnJrnl path (specifically within the $J alternate data stream), it was originally created by Microsoft to help applications like the Windows Indexing Service and file replication systems efficiently track what has changed on a disk without needing to scan the entire file system. Whenever a file is created, deleted, modified, or renamed, a record detailing the reason for the change and the exact timestamp is appended to the USN Journal.
For a DFIR investigator, the USN Journal serves as a high-fidelity historical ledger of file activity that bridges the gaps left by other artifacts. While the $MFT tracks the current state of a file (and can sometimes recover deleted file metadata), its records can eventually be overwritten. The USN Journal, however, sequentially logs the actions taken on those files. This means an investigator can track the exact moment a malicious payload was dropped, executed, and subsequently deleted by an attacker attempting to cover their tracks. Because it logs specific operation types (like USN_REASON_FILE_CREATE or USN_REASON_FILE_DELETE), it provides a highly reliable chronological timeline of data manipulation.
Enterprise Forensic Applications
The USN Journal is unparalleled in its ability to expose rapid data staging and anti-forensic techniques. In Insider Risk and HR Investigations, TensorGuard automates the parsing of the $UsnJrnl to identify if an employee rapidly created, compressed, and deleted massive amounts of proprietary files in a short time frame, even if those files no longer exist in the $MFT or the Recycle Bin. Furthermore, during Proactive Compromise Assessments, fleet-wide USN Journal analysis is highly effective at identifying the distinct, rapid read/write/rename patterns characteristic of active ransomware encryption or automated data exfiltration scripts.
Collecting, Decoding, and Viewing “USN Journal” with TensorGuard
- Create a TensorGuard account and sign in to the TensorGuard console at https://app.tensorguard.com.
- Select “Case Manager”, then the plus button to create a case. This will contain your enrolled devices, their reports, and any manually submitted collections.
- Linked inside the case menu, download the TensorGuard Forensic Collector and run it on your target system.
- In the console, click the plus button for “New Enrollment”, copy the enrollment key, and paste it into the TensorGuard Forensic Collector on your target device.
- Now that you have a device enrolled, select the device(s), and click “Send Signal”. Answer the questions regarding what you want to look for in the analysis, any alerting on positive findings, and if the collection and analysis should be recurring.
- Once the report is generated, you’ll have USN Journal delivered in the browser, alongside an executive summary and timeline of findings.
Get Started
TensorGuard™ is a trademark of TensorGuard Inc. All other trademarks are the property of their respective owners. The information provided on this blog is for educational and informational purposes only and does not constitute legal, forensic, or professional advice. Due to the complexities of Digital Forensics and potential legal implications, you should always consult with qualified legal counsel or a certified digital forensics expert before taking action based on findings.

USN Journal
Windows
A hidden system log that records changes made to files and directories, revealing a timeline of file creation, modification, and deletion.
About USN JournalStart with a Compromise Assessment.
The best way to see the power of TensorGuard is to use it. For a simple, flat fee, we will conduct a full, AI-powered Compromise Assessment on a selection of your critical systems.