What is the “Scheduled Tasks” Windows forensic artifact?
Windows Scheduled Tasks are a built-in administrative feature of the Windows operating system designed to automate the execution of programs, scripts, or system commands at predefined times or in response to specific system events. The configurations for these tasks are stored in two primary locations: as individual XML files within the %SystemRoot%\System32\Tasks\ directory, and as binary entries within the Windows Registry under the HKLM\SOFTWARE\Microsoft\Windows NT\CurrentVersion\Schedule\TaskCache key. These files and keys define everything about a task, including what executable to run, the command-line arguments to supply, the user context it should execute under (such as the highly privileged SYSTEM account), and the specific time or event triggers that initiate the task.
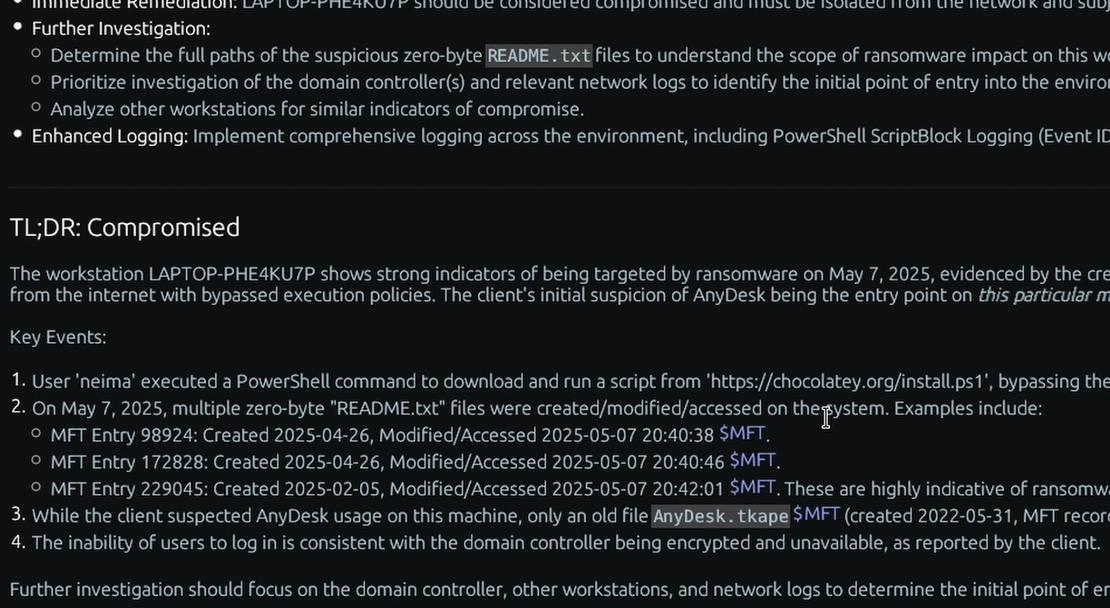
For a DFIR investigator, Scheduled Tasks represent one of the most critical locations to hunt for malicious persistence. Because it is a native, highly reliable mechanism, advanced persistent threats (APTs) and ransomware operators heavily abuse Scheduled Tasks to ensure their payloads survive system reboots and execute seamlessly under the radar. By analyzing these XML files and registry keys, an investigator can uncover exactly which commands an attacker scheduled, the specific trigger conditions they relied on, and the timestamp of when the persistence mechanism was created. This allows forensic analysts to trace the execution of fileless malware, uncover malicious scripts hidden within seemingly benign operations, and definitively prove how an attacker maintained their foothold over time.
Enterprise Forensic Applications
Scheduled Tasks analysis is essential for uncovering stealthy attacker footholds across a large-scale environment. During Proactive Compromise Assessments, TensorGuard automates the extraction and parsing of these task entries across the enterprise to instantly surface anomalous administrative scripts, unauthorized scheduled PowerShell commands, and dormant ransomware triggers. This capability allows security teams to rapidly identify persistence mechanisms that easily bypass traditional live endpoint monitoring, enabling immediate containment and a fundamental disruption of the adversary’s attack lifecycle.
Collecting, Decoding, and Viewing “Scheduled Tasks” with TensorGuard
- Create a TensorGuard account and sign in to the TensorGuard console at https://app.tensorguard.com.
- Select “Case Manager”, then the plus button to create a case. This will contain your enrolled devices, their reports, and any manually submitted collections.
- Linked inside the case menu, download the TensorGuard Forensic Collector and run it on your target system.
- In the console, click the plus button for “New Enrollment”, copy the enrollment key, and paste it into the TensorGuard Forensic Collector on your target device.
- Now that you have a device enrolled, select the device(s), and click “Send Signal”. Answer the questions regarding what you want to look for in the analysis, any alerting on positive findings, and if the collection and analysis should be recurring.
- Once the report is generated, you’ll have Scheduled Tasks delivered in the browser, alongside an executive summary and timeline of findings.
Get Started
TensorGuard™ is a trademark of TensorGuard Inc. All other trademarks are the property of their respective owners. The information provided on this blog is for educational and informational purposes only and does not constitute legal, forensic, or professional advice. Due to the complexities of Digital Forensics and potential legal implications, you should always consult with qualified legal counsel or a certified digital forensics expert before taking action based on findings.

Scheduled Tasks
Windows
A native Windows feature used to automate execution, frequently abused by adversaries for stealthy persistence and lateral movement.
About Scheduled TasksStart with a Compromise Assessment.
The best way to see the power of TensorGuard is to use it. For a simple, flat fee, we will conduct a full, AI-powered Compromise Assessment on a selection of your critical systems.