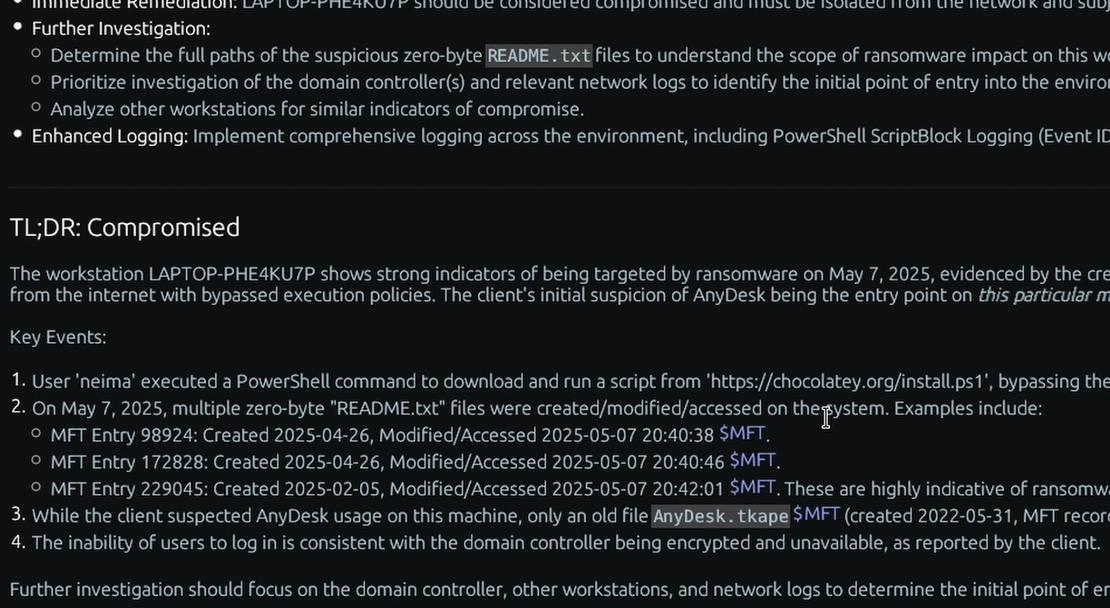
What is the “Prefetch” Windows forensic artifact?
The Windows Prefetch artifact is a system-level mechanism designed by Microsoft to accelerate the boot process and application startup times. Located in the %SystemRoot%\Prefetch directory, the Windows Cache Manager monitors the first ten seconds of an application’s execution. It records the specific executable code, dynamic link libraries (DLLs), and files accessed during this launch window and saves this profile into a .pf file. The filename is comprised of the executable’s name followed by an eight-character hash of the path from which it was run (e.g., CMD.EXE-0A75A511.pf).
For a DFIR investigator, Prefetch is widely considered one of the most reliable and information-rich artifacts for proving program execution. Even if an attacker meticulously deletes a malicious payload or runs a portable tool from a temporary USB drive, the operating system will inherently generate a Prefetch file upon launch. These .pf files contain a wealth of metadata, including the original path of the executed program, a historical run count, and up to the last eight execution timestamps on modern Windows systems. Furthermore, because the file catalogs every file and directory accessed during the startup phase, investigators can map out an executable’s dependencies, identify hidden configuration files it called out to, or prove that it interacted with specific sensitive directories.
Enterprise Forensic Applications
Prefetch analysis is an indispensable component for detecting evasive malware, lateral movement, and unauthorized software usage. During Proactive Compromise Assessments, TensorGuard automatically parses the Prefetch directory across the enterprise to quickly surface the execution of renamed administrative utilities (like psexec.exe masquerading as svchost.exe), living-off-the-land binaries (LOLBins), or portable exfiltration tools. In incident response scenarios, reconstructing the timeline via Prefetch timestamps allows analysts to pinpoint the exact moment an adversary achieved execution, track the frequency of their activity, and identify the footprint of tools that have long since been wiped from the disk.
Collecting, Decoding, and Viewing “Prefetch” with TensorGuard
- Create a TensorGuard account and sign in to the TensorGuard console at https://app.tensorguard.com.
- Select “Case Manager”, then the plus button to create a case. This will contain your enrolled devices, their reports, and any manually submitted collections.
- Linked inside the case menu, download the TensorGuard Forensic Collector and run it on your target system.
- In the console, click the plus button for “New Enrollment”, copy the enrollment key, and paste it into the TensorGuard Forensic Collector on your target device.
- Now that you have a device enrolled, select the device(s), and click “Send Signal”. Answer the questions regarding what you want to look for in the analysis, any alerting on positive findings, and if the collection and analysis should be recurring.
- Once the report is generated, you’ll have Prefetch delivered in the browser, alongside an executive summary and timeline of findings.
Get Started
TensorGuard™ is a trademark of TensorGuard Inc. All other trademarks are the property of their respective owners. The information provided on this blog is for educational and informational purposes only and does not constitute legal, forensic, or professional advice. Due to the complexities of Digital Forensics and potential legal implications, you should always consult with qualified legal counsel or a certified digital forensics expert before taking action based on findings.

Prefetch
Windows
A performance-enhancing artifact that provides definitive proof of application execution, run counts, and the specific files accessed during launch.
About PrefetchStart with a Compromise Assessment.
The best way to see the power of TensorGuard is to use it. For a simple, flat fee, we will conduct a full, AI-powered Compromise Assessment on a selection of your critical systems.