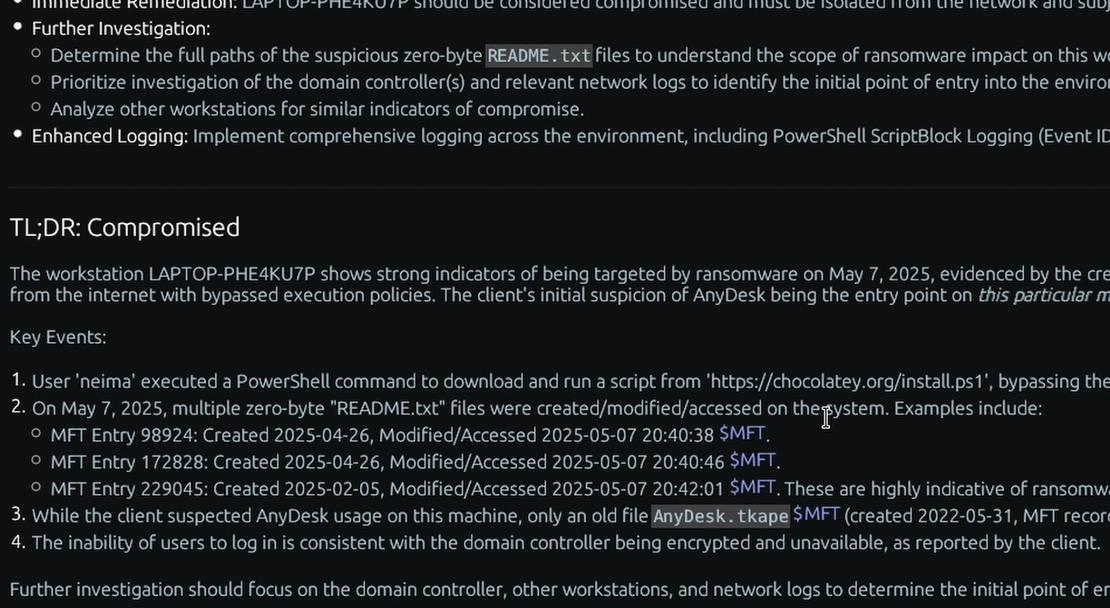
What is the “BAM/DAM” Windows forensic artifact?
The Background Activity Moderator (BAM) and Desktop Activity Moderator (DAM) are Windows services introduced in Windows 10 and Windows 8, respectively. Their primary function is to control the background activity of applications to optimize system resources and preserve battery life. To manage this, the operating system quietly records whenever an executable is launched. These records are housed deep within the system’s core configuration, stored in the SYSTEM registry hive under SYSTEM\CurrentControlSet\Services\bam\State\UserSettings\ and SYSTEM\CurrentControlSet\Services\dam\UserSettings\.
For a DFIR investigator, BAM and DAM are exceptional artifacts for identifying program execution and assisting with user attribution. Underneath these registry keys, Windows creates a subfolder for every User Security Identifier (SID) that logs into the machine. Within those specific SID folders, the registry logs the full absolute path of the executed file alongside a timestamp detailing when it was last run. Because BAM/DAM entries can persist even if the original file is deleted, and because they link the executed binary to a specific user account, they offer compelling evidence regarding which account executed a file and when.
Enterprise Forensic Applications
BAM and DAM serve as highly resilient mechanisms for reconstructing attacker timelines. During Proactive Compromise Assessments, TensorGuard leverages BAM/DAM as a powerful fallback when sophisticated adversaries actively clear the Prefetch directory or attempt to manipulate traditional execution logs. Furthermore, during Insider Risk and HR Investigations, because BAM data is organized by user SID, investigators can build a strong case showing that a specific user account executed an unauthorized wiping utility or portable exfiltration tool, providing critical context when navigating claims that “malware” or an unauthorized third party ran the file.
Collecting, Decoding, and Viewing “BAM/DAM” with TensorGuard
- Create a TensorGuard account and sign in to the TensorGuard console at https://app.tensorguard.com.
- Select “Case Manager”, then the plus button to create a case. This will contain your enrolled devices, their reports, and any manually submitted collections.
- Linked inside the case menu, download the TensorGuard Forensic Collector and run it on your target system.
- In the console, click the plus button for “New Enrollment”, copy the enrollment key, and paste it into the TensorGuard Forensic Collector on your target device.
- Now that you have a device enrolled, select the device(s), and click “Send Signal”. Answer the questions regarding what you want to look for in the analysis, any alerting on positive findings, and if the collection and analysis should be recurring.
- Once the report is generated, you’ll have BAM/DAM delivered in the browser, alongside an executive summary and timeline of findings.
Get Started
TensorGuard™ is a trademark of TensorGuard Inc. All other trademarks are the property of their respective owners. The information provided on this blog is for educational and informational purposes only and does not constitute legal, forensic, or professional advice. Due to the complexities of Digital Forensics and potential legal implications, you should always consult with qualified legal counsel or a certified digital forensics expert before taking action based on findings.

BAM/DAM
Windows
A Windows registry artifact that reliably tracks executed programs and links them directly to the specific user account that ran them.
About BAM/DAMStart with a Compromise Assessment.
The best way to see the power of TensorGuard is to use it. For a simple, flat fee, we will conduct a full, AI-powered Compromise Assessment on a selection of your critical systems.