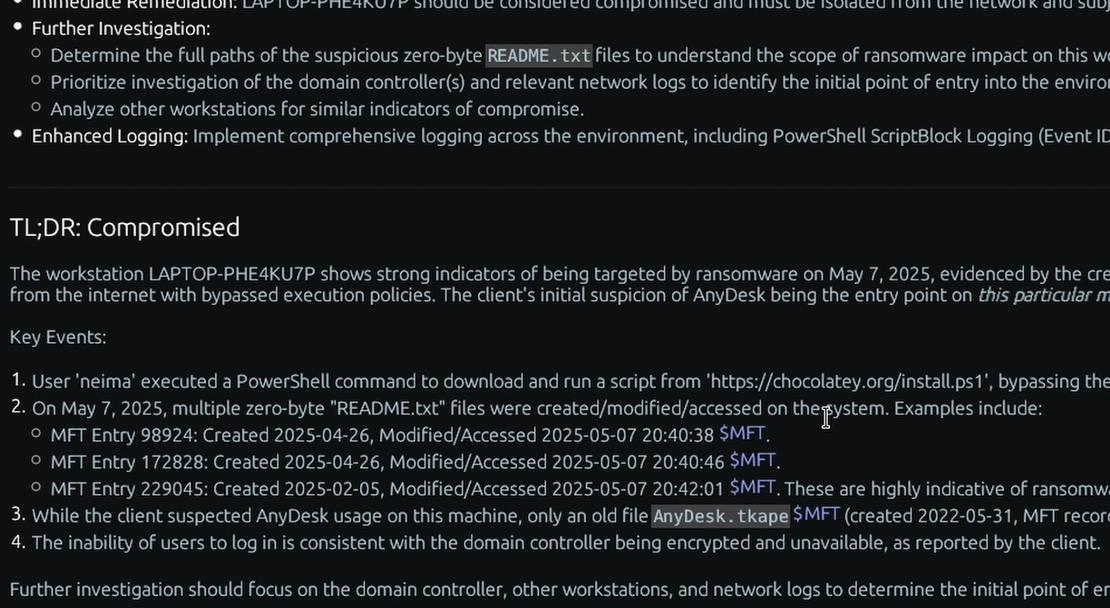
In this technical breakdown, we examine an anonymized “Positive” insider threat incident analyzed by the TensorGuard platform, demonstrating how automated correlation of Windows artifacts rapidly identifies data staging and exfiltration.
For digital forensic investigators, proving an insider threat requires an airtight timeline. When an employee is suspected of intellectual property theft, relying on firewall logs or EDR telemetry is rarely enough. The investigator must prove intent and execution on the endpoint itself.
Historically, this required manually extracting registry hives, parsing the Master File Table ($MFT), and writing custom scripts to correlate timestamps. TensorGuard automates this entire process.
The Trigger: Correlating Network Activity with Endpoint Execution
In this engagement, a user was suspected of anomalous behavior immediately following an HR disciplinary action. EDR had not triggered any alerts, as the user was utilizing legitimate, “living-off-the-land” techniques.
Upon ingesting the forensic .spade package into the TensorGuard console, the AI engine immediately cross-referenced the user’s Web Browser artifacts with the AmCache.
The timeline generation revealed absolute temporal synchronicity:
- 16:35:06: The user accessed an email titled “Performance Improvement Plan” via their web browser.
- 16:35:06: At that exact second, the
AmCache.hverecorded the execution of7z.exe(a third-party compression utility not standard to the corporate build). - 16:35:06: Simultaneously,
AmCache.hvelogged the insertion of a SanDisk USB removable media device.
By automatically parsing the AmCache, TensorGuard established the initiation of a coordinated, premeditated exfiltration event without the need for manual timeline reconstruction.
Proving Data Staging via the $MFT and ShellBags
Executing 7z.exe is suspicious, but we must prove what was compressed.
TensorGuard’s automated $MFT parser identified a massive file creation event. An $MFT record pointed to the creation of Archive.zip on the user’s Desktop, sized at 3.3 GB.
To prove the user interacted with this file, TensorGuard cross-referenced the ShellBags artifacts located within the NTUSER.DAT registry hive.
Exposing Anti-Forensics
Insiders frequently attempt to cover their tracks. In this case, the Archive.zip file was no longer present on the live file system.
However, because TensorGuard reads the raw $MFT, it identified that the file record had simply been marked as inactive (deleted). Furthermore, an examination of the Windows AutomaticDestinations (Jump Lists) yielded zero results for that date, strongly indicating deliberate log clearing. This was corroborated by the browser history, where TensorGuard flagged searches for “how to copy files without being detected.”
From Raw Hex to Executive Intelligence
To parse the $MFT, AmCache, ShellBags, Jump Lists, and Browser SQLite databases manually across a device would take a senior examiner hours, if not days, to document properly.
TensorGuard processed these artifacts, linked the citations to the raw hex/CSV data for verifiable proof, and generated a C-Suite ready report outlining the exfiltration vectors in under 10 minutes. By operationalizing these deep technical artifacts, security teams can drastically accelerate their Time-to-Certainty.