Table of Contents
While the cybersecurity industry frequently focuses on the theoretical capabilities of Artificial Intelligence, the true measure of a Next-Gen AI Incident Response platform lies in its operational reality. Having access to deep, historical forensic data is only half the battle; the speed, fluidity, and collaborative nature of how your security team interacts with that data determines whether an adversary is neutralized in minutes or months.
At TensorGuard, we recognize that Enterprise Security Operations Centers (SOCs) and incident response teams require a platform that adapts to their specific governance requirements and actively enhances their daily workflow. By moving beyond raw data extraction, TensorGuard delivers an unparalleled, interactive investigative experience.
Here is a look under the hood at the actual workflow of the TensorGuard platform.

1. Flexible Deployment: Built for Your Architecture
Enterprise and government environments are incredibly complex, and data residency requirements dictate strict governance over where forensic data can reside. A rigid, one-size-fits-all SaaS model is fundamentally incompatible with the needs of highly regulated industries.
To accommodate this, TensorGuard offers unparalleled deployment flexibility, ensuring your organization maintains absolute control over its sensitive forensic artifacts.
- Public Cloud vs. On-Premises: By default, TensorGuard operates as a secure, highly available cloud platform. However, for organizations with strict data sovereignty mandates, defense contractors, or critical infrastructure providers, TensorGuard can be hosted entirely inside your own on-premises infrastructure for a small premium. You retain the exact same powerful AI capabilities without your data ever crossing your perimeter.
- Web and Native Client Parity: Analysts can access the TensorGuard Console via any modern web browser for immediate triage from anywhere in the world. For power users conducting deep, multi-day investigations, we offer a dedicated Native Client. Both environments boast 100% feature parity, though the native application can more efficiently utilize local system resources for intensive visual rendering.
2. Centralized Case Management & Team Collaboration
Modern Digital Forensics and Incident Response (DFIR) is not a solo endeavor. It is a highly collaborative discipline requiring seamless communication between Tier 1 analysts, senior threat hunters, and legal counsel.
Traditional forensics often involves passing massive CSV files or raw disk images back and forth, leading to version control nightmares and siloed intelligence. TensorGuard fundamentally democratizes this process through Centralized Case Management.
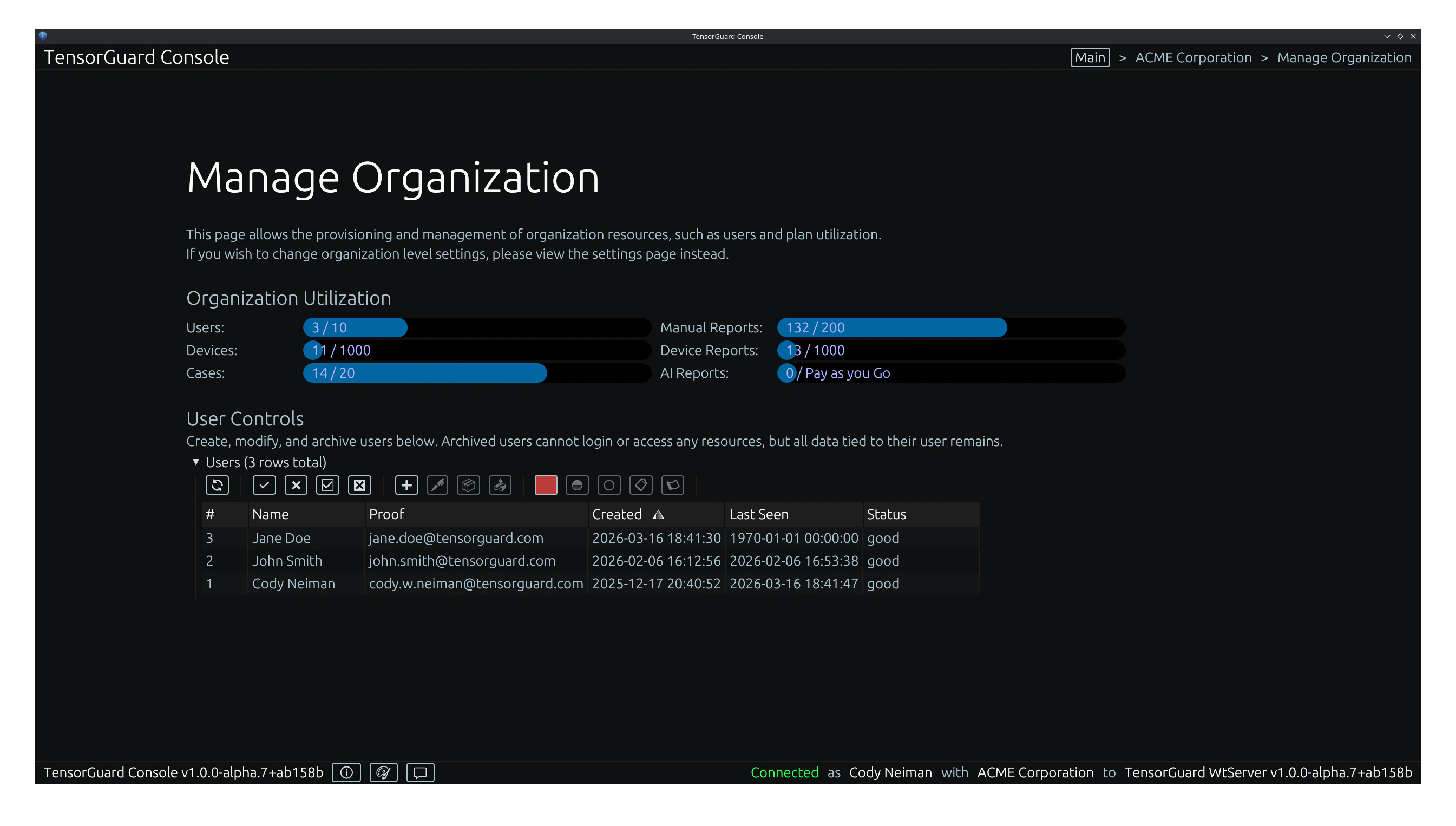
When a new investigation is launched—whether it is an M&A due diligence sweep or an insider threat inquiry—administrators can provision a dedicated “Case” workspace.
- Granular Access Controls: Securely assign specific team members to specific cases. This ensures that a highly sensitive HR investigation remains strictly compartmentalized from the broader SOC team’s daily alert triage.
- Shared Intelligence and Tagging: TensorGuard acts as the single source of truth for the investigation. We utilize shared organizational settings, such as custom table highlight color palettes. If a Tier 1 analyst identifies a suspicious
AmCacheexecution event and tags it in red, that highlight is instantly visible to the senior investigator reviewing the case, communicating intent without needing to draft an email or update a ticketing system.
3. The Interactive Analyst Experience: Visualizing the Timeline
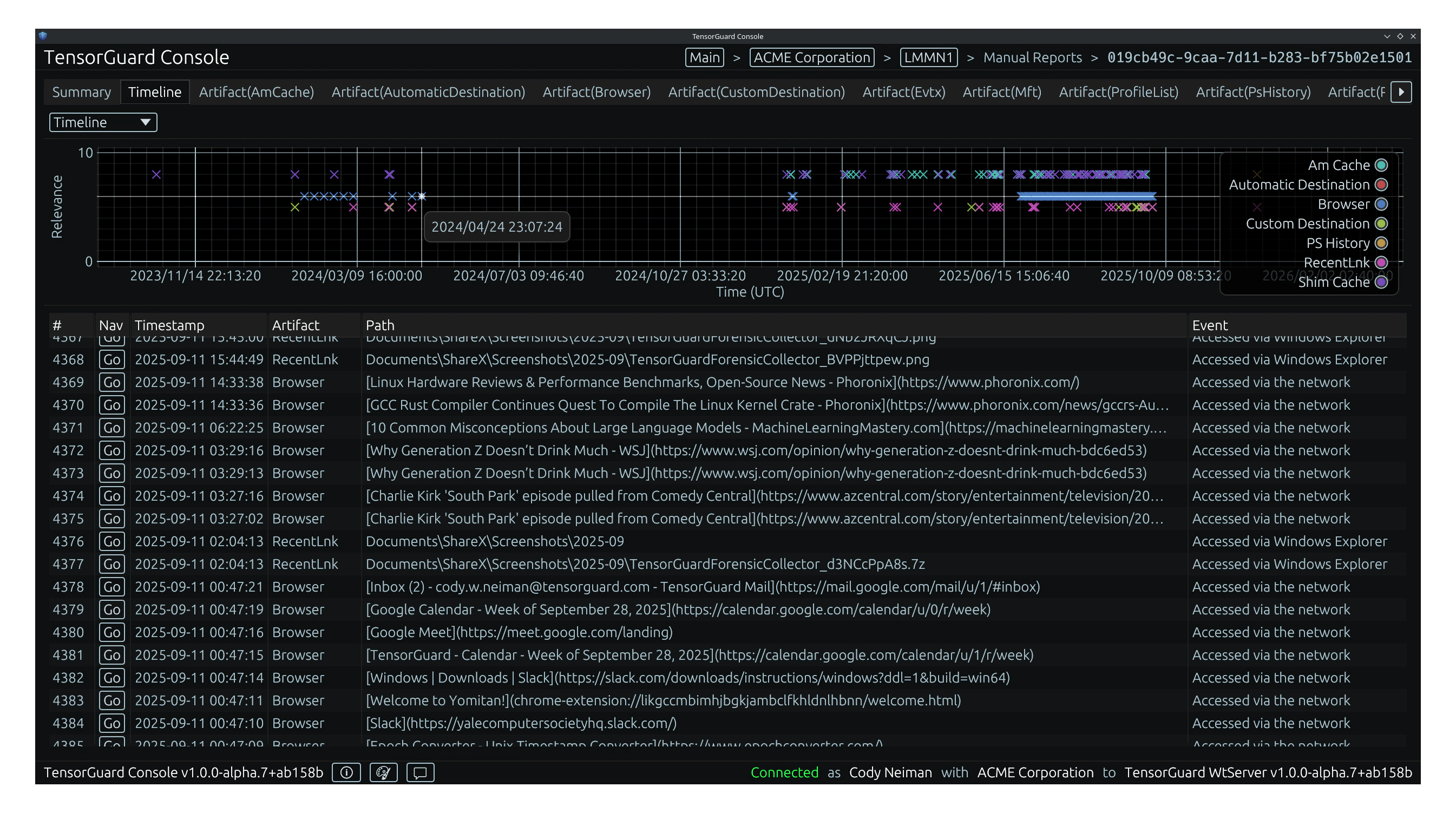
The core of the TensorGuard workflow is the Interactive Timeline Analysis.
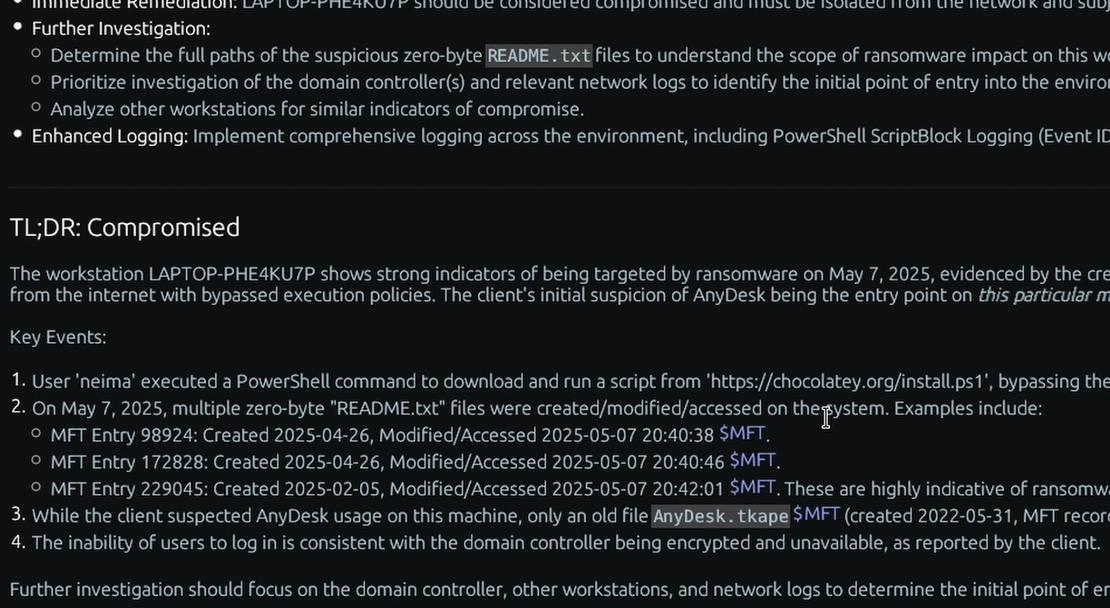
Rather than forcing analysts to manually stitch together disparate artifacts using command-line utilities or static spreadsheets, the Evie Intelligence Engine parses millions of rows of data—from the $MFT to the ShellBags—and synthesizes them into a single, unified, chronological timeline.
- Activity Hotspots: The timeline graph instantly visualizes periods of high system activity. A sudden spike in
$MFTfile creations combined with outbound network usage (SRUM) creates a visual “hotspot,” immediately directing the analyst’s attention to the exact moment of potential data exfiltration. - Fluid Navigation: Analysts can drag, zoom, and hover over the timeline to rapidly narrow their investigative window from months down to specific milliseconds.
- Artifact Filtering: Need to filter out standard Windows OS noise? With a single click, investigators can isolate specific artifact types—such as only showing
PS HistoryandEvtxlogs—to track a Living-off-the-Land (LotL) attack without distraction.
Most importantly, this fluid visual interface never obscures the underlying ground truth. When the analyst clicks on an AI-generated event on the timeline, TensorGuard instantly opens the corresponding raw hex or CSV data in the lower pane. You are always one click away from the cryptographically sound evidence required for legal defensibility.
4. Automated, Recurring Sweeps: Continuous Validation
Having deep historical visibility is powerful, but manually running queries still requires human initiative. TensorGuard turns forensics into a continuous, proactive validation program through Automated, Recurring Sweeps.
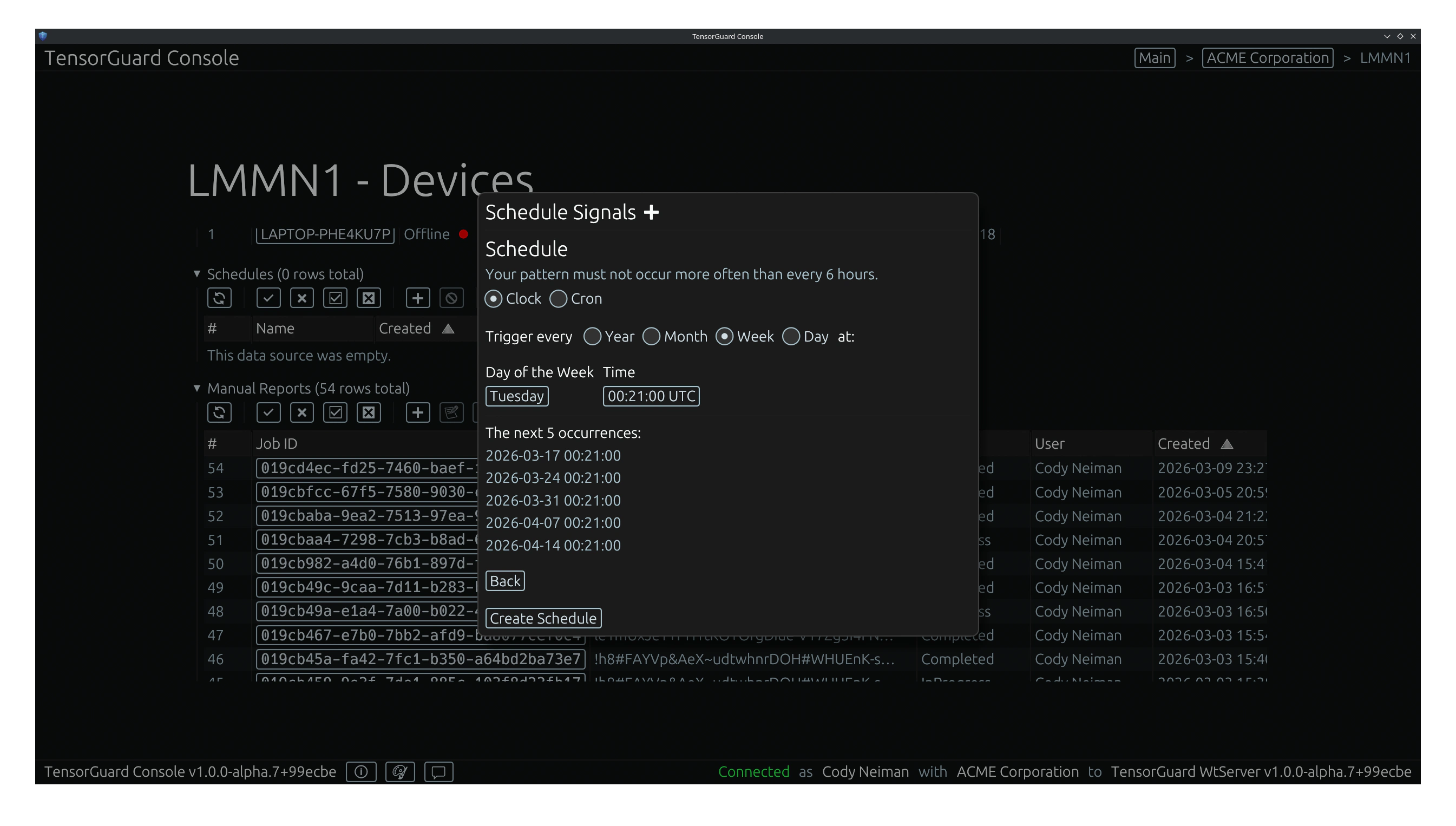
Security teams can configure scheduled sweeps to run daily, weekly, or as frequently as every 6 hours. These schedules can be tied directly to specific AI alignment presets—such as “Compromise Assessment,” “Insider Threat,” or “M&A Due Diligence.” This empowers your SOC to establish a baseline of normal activity and automatically sweep critical servers or executive laptops for dormant threats while the team is asleep, completely eliminating the reliance on ad-hoc, manual threat hunting.
Elevating the SOC Workflow
By combining flexible deployment, robust case management, recurring automation, and an incredibly intuitive visual interface, TensorGuard eliminates the friction of traditional digital forensics.
Security is no longer constrained by the limitations of live-only telemetry or the massive costs of manual data formatting. Welcome to the next generation of incident response.