In the modern security stack, Endpoint Detection and Response (EDR) provides essential real-time defense, while traditional digital forensics offers unmatched depth during a critical incident. However, a crucial operational gap exists between them.
Why TensorGuard?
Security teams are constantly forced to make a trade-off: the broad, live-only visibility of EDR, or the deep, evidence-based analysis of forensics that is too slow and expensive to deploy at scale. This leaves most systems unexamined at a forensic level, creating vast blind spots where sophisticated or historical threats can dwell undetected.
TensorGuard was built to eliminate this compromise.
We operationalize digital forensics, fusing its evidence-based certainty with the scale and automation of a modern cloud platform. Our AI engine transforms vast amounts of raw historical data from your endpoints into clear, actionable intelligence—complete with executive summaries, timelines, and remediation advice. This empowers you to move beyond reactive firefighting and proactively hunt for threats, continuously assess your environment for compromise, and get evidence-backed answers to critical questions across your entire fleet.
TensorGuard
TensorGuard is a next-generation, AI-driven, Digital Forensic and Incident Response platform built on state of the art large data processing methods.
A New Paradigm: From Reactive to Proactive Forensics
Historically, digital forensics has been a reactive, costly, and manual process, reserved for major incidents. This meant that deep investigations were limited to a handful of critical systems, while the rest of your fleet remained a black box.
TensorGuard changes this paradigm. By combining automated, remote forensic collection with a powerful AI-driven analysis engine, we transform forensics into a proactive security function. You can now establish a baseline of normal activity, hunt for threats, and assess your entire organization’s security posture on a continuous basis. Our platform automates the collection and analysis of forensic data, allowing you to quickly identify potential threats and vulnerabilities without the need for extensive manual effort.
Automated Compromise Assessment at Any Scale
TensorGuard enables you to conduct comprehensive compromise assessments across your entire fleet, regardless of size.
Uncover the Complete History of Your Endpoints
Endpoint Detection and Response (EDR) tools are essential, but they primarily see what happens after they are installed. TensorGuard complements these tools by looking backward.
This makes Compromise Assessments more than just a snapshot in time. With the first collection, you can uncover evidence of long-dormant threats or historical compromises, giving you an unparalleled understanding of your true security state.
Complete History
Our technology analyzes forensic artifacts that can date back years, providing insight into system activity long before TensorGuard was ever deployed.
Intelligence, Not Just Data
Raw forensic data is overwhelming and requires specialized expertise to interpret. Our platform does the heavy lifting for you.
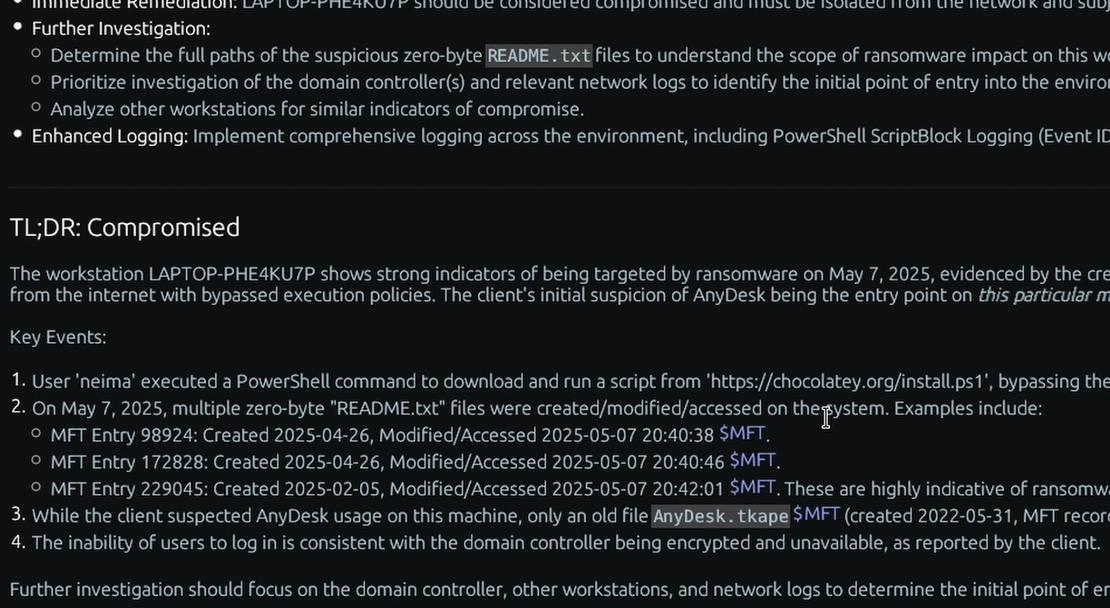
- AI-Powered Reporting: Our contextual analysis engine processes forensic artifacts into clear, actionable intelligence. You receive executive summaries, timelines of suspicious events, and suggested remediation steps, all supported by direct evidence you can review yourself.
- Empowering Internal Teams: We group complex data into simple “Indicators” (e.g., Program X was executed, User Y accessed File Z). This empowers your internal security team to conduct meaningful investigations without needing to be forensics experts.
Actionable Evidence
Our platform transforms raw forensic data into clear, actionable intelligence, complete with executive summaries, timelines, and remediation advice.
Answer Critical Questions On Demand
Our platform’s greatest strength lies in its ability to conduct targeted investigations at scale. You can move beyond predefined alerts and ask specific questions about your environment, receiving evidence-backed answers in minutes.
- “Do a compromise assessment for these devices every week. We’re especially concerned about the possibility of ransomware.”
- “The users of these devices are soon leaving the company. Keep an eye on them for any suspicious activity related to accessing or exfiltrating sensitive data.”
- “Has the tool
mimikatz.exeor other common hacking tools ever been run on these domain controllers?” - “Which applications generated the most network traffic last month across our sales team’s laptops?”
- “Show me all devices where a USB drive was connected in the last 72 hours.”
This capability allows you to rapidly jumpstart investigations, hunt for specific threats, and gain granular visibility across any number of devices.
Plain Language Queries
Our technology enables you to ask questions and generate reports in plain language, making it easy to get the information you need without needing to know complex query languages.
Illuminate the Insider Threat
Malicious or negligent insiders often use legitimate tools and access to conduct unauthorized activity, bypassing traditional prevention-focused security controls. Because TensorGuard analyzes the full history of user and system activity, it is uniquely positioned to detect these threats. By understanding baseline behaviors, you can easily identify anomalies that may indicate policy violations, data exfiltration, or other insider-driven risks.
Behavioral Anomaly Detection
We use complex behavioral patterns to flag anomalies, enabling you to detect insider threats that traditional security tools might miss.
Next Steps
By integrating TensorGuard into your security architecture, you gain a powerful, evidence-based view into the past, present, and future security of your endpoints. 🚀
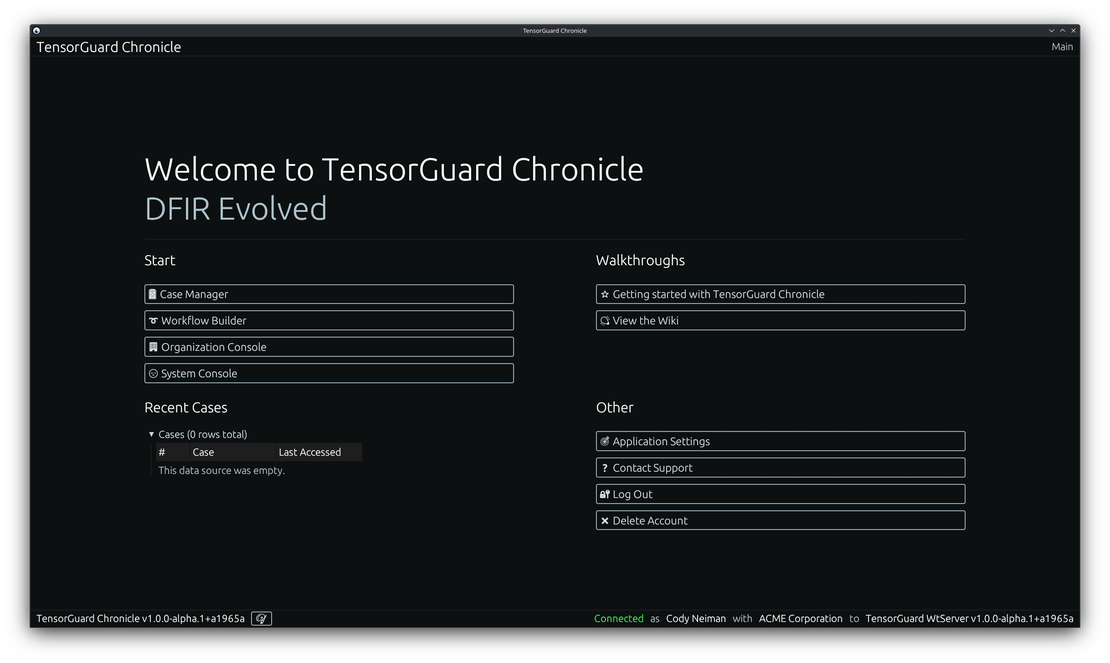
Continue along with the documentation to:
- Download and access TensorGuard
- Create your first case
- Enroll a device
- Take a service or manual forensic collection
- Generate a report
- Set a schedule for automated analysis
- …and more!