Table of Contents
In the high-stakes arena of Corporate Development and Private Equity, inheriting a target company’s technology stack is often the greatest source of undocumented financial liability.
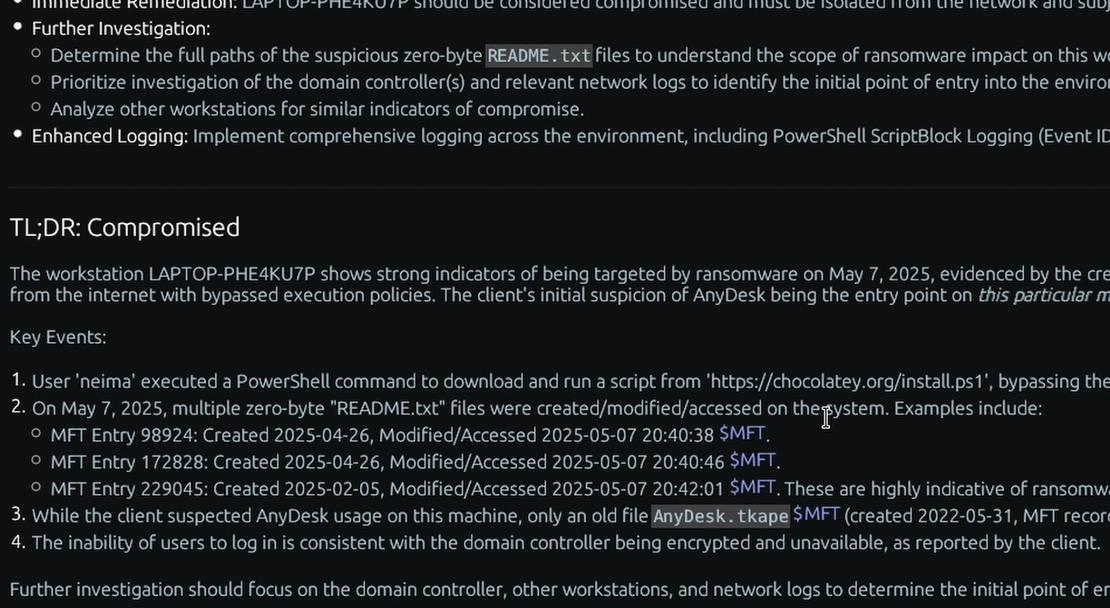
Traditionally, M&A cyber due diligence relies heavily on compliance questionnaires, executive interviews, and a review of the target’s current real-time security dashboards. This methodology possesses a massive, potentially catastrophic flaw: checking a compliance box fails to uncover a threat actor waiting patiently for network integration.
What if the target company was compromised six months ago, and an Advanced Persistent Threat (APT) is lying dormant, waiting for the acquisition to connect their compromised network to your pristine enterprise architecture? When engaging in cybersecurity mergers and acquisitions, real-time security tools only show what is happening right now. To protect your investment and ensure you are not inheriting a breach, you must assess the historical ground truth.
The Flaw in Traditional IT Audits
When evaluating a target company, their existing Endpoint Detection and Response (EDR) telemetry is inherently biased. If a sophisticated adversary bypassed their EDR months ago utilizing “living-off-the-land” techniques, the live dashboard will show a clean bill of health.
You cannot rely on the target’s tools to audit the target’s security. To survive post-acquisition scrutiny and accurately gauge M&A security risk, Corporate Development teams and Legal Counsel require undeniable, artifact-based proof of the network’s historical integrity before a single cable is connected.

Rapid, Quiet Deployment with TensorGuard
M&A timelines are exceptionally tight, and absolute secrecy during the “quiet period” is paramount. A multi-week manual Incident Response engagement is disruptive, slow, and alerts the target company’s broader staff to the impending transaction.
TensorGuard resolves this by providing rapid, silent, and defensible compromise assessments at scale, acting as the ultimate target company compromise assessment.
- The
.spadePackage: TensorGuard’s lightweight, read-only collector can be seamlessly deployed across the target’s fleet without disrupting daily operations. It compiles an encrypted, immutable.spadepackage containing years of historical ground truth—from the$MFTto theShimCache. - Automated Triage: Once the forensic packages are uploaded to the TensorGuard Console, our Evie 2.0 Intelligence Engine parses the data in parallel. Within minutes, you receive a C-Suite-ready executive summary detailing any historical intrusions, dormant malware droppers, or severe compliance violations.
- Defensible Proof: Every finding generated by TensorGuard is directly cited to the raw hex/CSV data. You are provided with cryptographically sound evidence that can be leveraged directly in term negotiations or purchase price adjustments.
The Break-Even Probability: The Ultimate Insurance Policy
In the context of M&A economics, a TensorGuard Compromise Assessment is the most logical insurance policy a Corporate Development team can purchase.
Consider a standard $100M acquisition. Deploying a TensorGuard Enterprise Sweep across the target company’s critical infrastructure requires a negligible, flat-fee investment relative to the deal size.
If the assessment uncovers a historical breach or severe lack of security hygiene, allowing your legal counsel to negotiate a mere 1% price or terms adjustment, you have just saved $1,000,000. That represents an exponential return on investment on the cost of the initial sweep.
Ensure you aren’t inheriting a breach. Assess the historical ground truth before you connect their network to yours.
Maintaining Absolute Confidentiality with Centralized Case Management
In the high-stakes environment of corporate acquisitions, information control is just as critical as threat detection. Leaking the existence of an M&A due diligence investigation can jeopardize a multi-million dollar transaction or violate SEC regulations. Integrating target company telemetry into your primary Security Operations Center (SOC) queue exposes highly sensitive deal data to your broader security staff, creating an unacceptable risk of internal leaks.
TensorGuard was architected with these strict governance requirements in mind. Our platform features Centralized Case Management, which allows administrators to provision multiple “Cases” to create a natural division for different client engagements or investigations.
- Strict Compartmentalization: Organization administrators can create isolated case environments specifically for the target company’s data.
- Secure Access Control: You can assign specific, authorized users to specific cases.
- Need-to-Know Visibility: This ensures that analysts only see the data relevant to their work, keeping M&A telemetry strictly cordoned off from your daily operational alerts.

Overcoming Air-Gapped and Highly Sensitive Networks
Target companies often possess highly restricted enclaves—such as manufacturing control systems, R&D labs, or defense-related infrastructure—that are intentionally air-gapped from the public internet. Traditional EDR and live-telemetry agents require constant outbound internet connectivity to function, rendering them useless for auditing these critical offline assets during due diligence.
TensorGuard ensures that no segment of the target company’s infrastructure remains a blind spot. For air-gapped or highly sensitive systems, our platform offers flexible manual collection capabilities.
- Offline Acquisition: Investigators can physically or logically run the lightweight collector on the isolated target device to generate a secure, offline forensic package.
- Asynchronous Uploads: These encrypted packages can then be manually transferred and uploaded to the TensorGuard console for full AI analysis when convenient.
This guarantees that even the most deeply buried, offline assets are forensically audited before you sign the final purchase agreement.

Time-to-Certainty at Enterprise Scale
M&A transactions operate on notoriously unforgiving timelines. Extending the quiet period by weeks to accommodate a traditional digital forensics firm is rarely an option. However, relying on manual triage is mathematically unfeasible within a standard due diligence window.
Conducting manual triage for 1,000 devices can take a single analyst over 20 weeks. A deal simply cannot wait that long for security validation.
TensorGuard acts as a massive force multiplier, fundamentally collapsing the time from suspicion to certainty. Once the forensic artifacts are collected, TensorGuard’s analysis for 1,000 devices in as little as 10 minutes. This unprecedented operational speed allows your deal team to bypass tedious data collection and focus immediately on evaluating confirmed threats and adjusting the deal terms accordingly.