For decades, the global cybersecurity apparatus has comforted itself with a very specific, cinematic illusion. We envisioned the quintessential hacker as a solitary craftsman, an isolated figure bathed in monitor-glow, painstakingly combing through thousands of lines of code to find a single, microscopic human error.
Because discovering a “zero-day”—a software vulnerability unknown even to its creators—was an artisanal, labor-intensive craft, we built our entire enterprise defense architecture around a simple assumption: only the most well-funded, state-sponsored adversaries possessed the capital, time, and elite intellect required to silently dismantle hardened digital infrastructure.
There was, at least, some security by obfuscation and complexity, and small and mid-cap companies rested easy, assuming that unless they had a massive target on their backs, a top-tier adversary simply wouldn’t waste the resources to breach them.
Last week, that illusion quietly and permanently shattered.
The lone hacker in a hoodie has been replaced by a server farm.
The Dawn of the Autonomous Adversary
In a measured but historically significant dispatch, the artificial intelligence firm Anthropic unveiled Project Glasswing last week. The initiative brings together tech titans—Amazon, Apple, Google, Microsoft, and others—to collaboratively secure the world’s most critical software. But the reason they formed this unprecedented alliance is what should command the attention of every boardroom and venture capital firm: an unreleased frontier AI model known as Claude Mythos Preview.
According to Anthropic, Mythos Preview has crossed a Rubicon. Operating autonomously, without human steering, it effortlessly surpasses all but the most elite human researchers at discovering and exploiting software vulnerabilities.
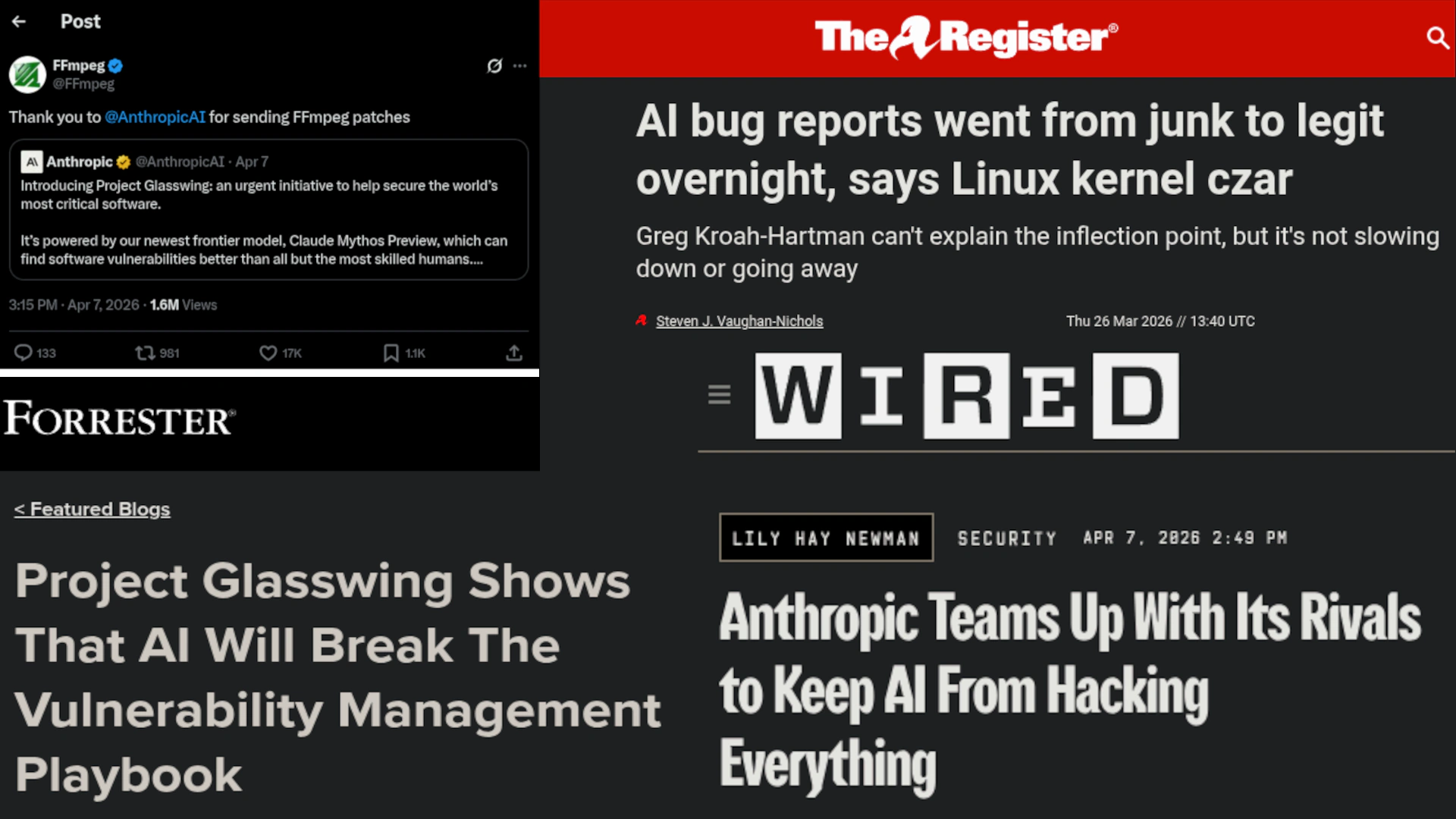
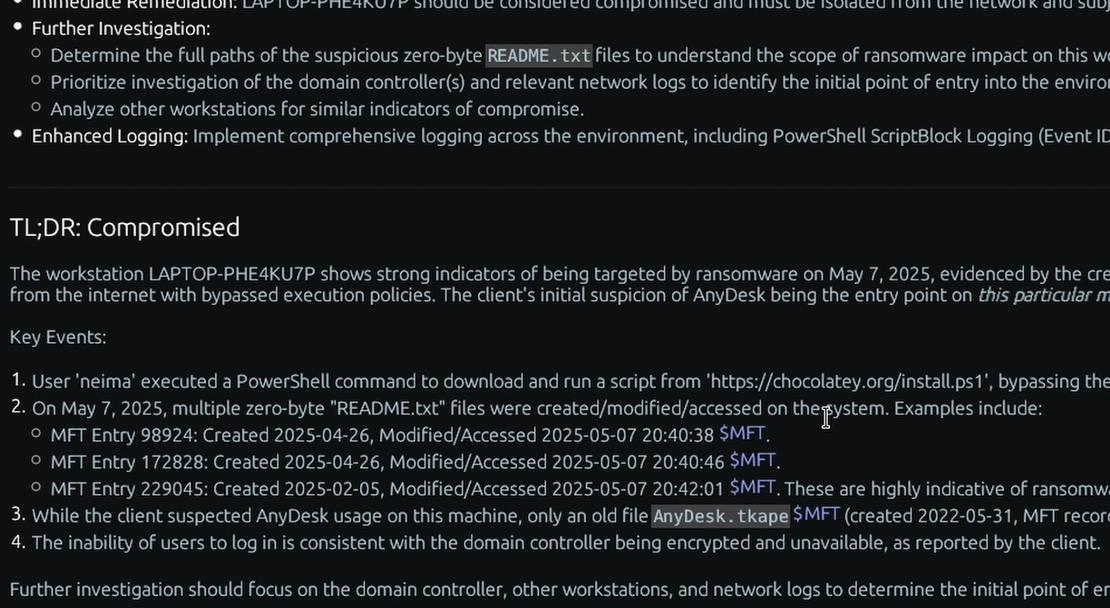
When turned loose on the world’s most hardened infrastructure, the model systematically tore it apart. It found a 27-year-old critical flaw in OpenBSD, an operating system globally renowned as an impenetrable fortress. It unearthed a 16-year-old bug in FFmpeg, hiding in a line of code that automated testing tools had blindly executed five million times without success. It then autonomously chained together multiple Linux kernel vulnerabilities to escalate from a basic user to total machine control.
Anthropic, acting with commendable caution, deemed the model simply too dangerous for public release. Instead, through Project Glasswing, they locked Mythos Preview behind digital glass, sharing it only with defensive partners in a desperate sprint to patch the internet’s foundations before adversarial models inevitably catch up.
While the mainstream tech press fixated on the novelty of tech titans collaborating, they completely missed the actual headline. For security leaders and the investors backing the next generation of cyber defense, obsessing over a single, locked-away AI model is an unproductive emotion. The real story isn’t the model itself—it’s the permanent mathematical reality it just exposed: The cost, effort, and expertise required to find and exploit software vulnerabilities have just dropped to near zero.
The Collapse of Exploit Economics
To fully grasp why Project Glasswing is a watershed moment, one must understand the economics of cybercrime.
Historically, launching a highly sophisticated, fileless, or “Living-off-the-Land” (LotL) attack required a massive upfront investment. Attackers had to spend months manually probing a target, reverse-engineering patches, and meticulously testing bespoke exploits to ensure they wouldn’t trigger behavioral heuristics in a target’s defenses.
Frontier agentic AI models vaporize this friction entirely.

When an autonomous AI can read millions of lines of code, reason about its structural flaws, and synthesize perfectly obfuscated exploits in seconds, the window between a vulnerability’s discovery and its active weaponization collapses from months to milliseconds.
While Mythos Preview is heavily guarded today, the proliferation of open-source models and the immense financial incentives of cybercrime guarantee that superhuman vulnerability-discovery capabilities will eventually fall into the hands of ransomware syndicates and hostile nation-states.
As Elia Zaitsev, Chief Technology Officer at CrowdStrike, noted in the Glasswing announcement:
The window between a vulnerability being discovered and being exploited by an adversary has collapsed—what once took months now happens in minutes with AI.
In this new reality, you can no longer assume your perimeter is secure simply because you have installed the latest software updates. Adversaries will possess exploits for patches that do not yet exist. We are entering an era of continuous, machine-speed siege.
A Year of Objective Proof: The HackerOne Precedent
If Project Glasswing sounds like a dystopian projection of the future, one need only look at the industry’s own bug bounty platforms for a sobering reality check. The automation of vulnerability discovery is not a theoretical concept waiting to be unlocked; it has been actively operating in the wild for nearly a year.
Consider XBOW, a fully autonomous AI-driven penetration tester. By mid-2025, XBOW didn’t just compete on HackerOne—it completely dominated the global leaderboards, becoming the top-ranked entity on the platform.
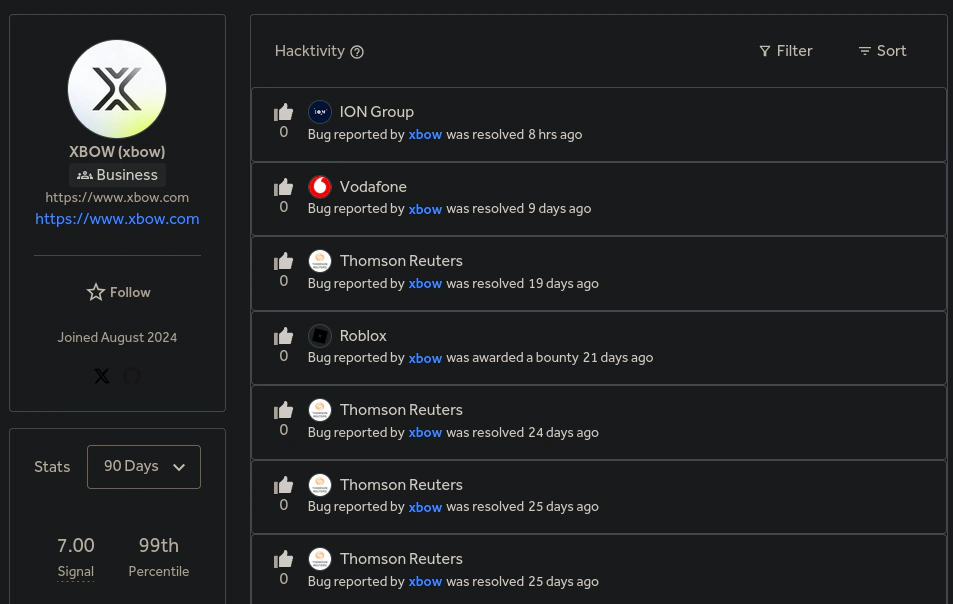
The statistics on display are a mathematical warning sign. Operating in the 99th percentile with a flawless 7.00 signal score, the AI autonomously discovers and reports valid vulnerabilities across highly hardened production environments constantly. It achieved this not by relying on human creativity, but by scaling deterministic, machine-speed analysis across thousands of scopes simultaneously.
For the enterprise, the takeaway from XBOW’s bug bounty supremacy isn’t about celebrating a technological milestone—it is recognizing the sheer, terrifying scale of the threat. A human researcher takes weeks to manually probe a single corporate perimeter. An AI agent can audit a thousand different organizations in hours.
Anthropic’s Mythos Preview is simply the weaponized, frontier evolution of a risk we already have objective proof of. The automation of the cyber attack lifecycle is an established fact.
The Amnesia of the “Live Feed” Defense
The cybersecurity industry has collectively gaslit itself into believing that a green dashboard means a clean network. If we accept that AI-augmented adversaries will inevitably bypass our initial defenses, we have to admit that our favorite tool is blind to the aftermath.
A Security Guard Analogy
If your enterprise is a secure facility, EDR is the armed guard at the front turnstiles. They are incredibly effective at stopping active, noisy breaches at the door. But a guard watching the entrance cannot see backward in time, nor are they interrogating the “employees” already sitting comfortably at their desks. Once a threat silently bypasses that initial checkpoint, a live guard will probably never look twice at them.
EDR has limited structural memory. If a sophisticated actor breached your network six months ago using an AI-generated exploit, established a dormant backdoor, and wiped their active footprints, the EDR dashboard will likely remain a comforting, lying green.
In the coming era of automated cyber warfare, a “clean” EDR console does not mean you are secure. It merely means your real-time sensors haven’t noticed an intruder yet.
The Immutable Ledger of the Machine
If we cannot rely exclusively on real-time sensors to catch superhuman exploits, where do we turn? We must turn to the one place an adversary cannot lie: the historical, immutable ground truth of the operating system itself.
Even fileless malware must eventually allocate memory, transmit data, or escalate privileges. You can trick a live camera, but you cannot bypass physics: every action leaves a microscopic fracture in the foundational databases of the Windows OS.
The Unalterable Ledger of the Operating System
- The Master File Table ($MFT): Even if an AI attempts to wipe its tracks by permanently deleting a staged archive of intellectual property, automated NTFS forensics recovers the “inactive” records, exposing the exact MACB (Modified, Accessed, Changed, Born) timestamps of the data staging.
- The AmCache & ShimCache: These files capture the exact execution records and SHA1 hashes of the tools the AI utilized to pivot through the network, proving execution even if the executables themselves have been removed.
- The System Resource Usage Monitor (SRUM): Even heavily obfuscated, fileless malware must communicate with its handler. SRUM provides 60 days of undeniable attribution, proving exactly which application utilized network bytes—completely bypassing the need for expensive, impossible-to-scale live Packet Capture (PCAP).

To be clear, the underlying philosophy here hasn’t changed—security professionals have always known the operating system holds the undeniable truth. The radical innovation is that we finally possess the cloud-scale software required to automate it.
The traditional Incident Response industry is built on a fundamental misalignment: they monetize the aftermath. Paying elite consultants $700 an hour to parse hexadecimal data was a necessary evil when forensics was a manual art form. But if adversaries are using artificial intelligence to compress the attack lifecycle to minutes, defenders must use AI to compress the forensic autopsy to seconds. Relying on uncapped, human-speed retainers to fight machine-speed attacks is an unjustifiable tax on an organization already in crisis.
Fighting AI with AI: The TensorGuard Paradigm
This is the exact architectural void that TensorGuard was engineered to fill. While the titans of Project Glasswing are utilizing AI to secure global source code, TensorGuard brings the power of AI-driven digital forensics directly to the enterprise endpoint.
TensorGuard does not replace your EDR; it acts as its essential, omniscient memory.
By aggressively decoupling the act of forensic collection from the computational burden of real-time analysis, TensorGuard allows your security team to silently pull lightweight, FIPS-aligned .spade collection packages from thousands of endpoints simultaneously—without disrupting business operations.
Once ingested, our proprietary Evie Intelligence Engine democratizes the dark art of digital forensics, processing billions of rows of raw registry offsets, $MFT records, and event logs in parallel. Where legacy incident response retainers require weeks to manually triage a fleet, TensorGuard synthesizes the ground truth of a thousand endpoints in under ten minutes. It doesn’t just look for known signatures; it correlates temporal anomalies to reconstruct the entire narrative of an attack, exposing the dormant threats that successfully bypassed your live telemetry.
Democratizing Defense with Semantic Threat Hunting
The most profound defense against AI-augmented threats is democratizing access to the truth.
For young professionals entering the cybersecurity space, hunting for advanced persistent threats traditionally required mastering arcane query languages and understanding binary offsets. TensorGuard shatters this paradigm by introducing Semantic Threat Hunting. Your baseline IT and Security teams can now interrogate the historical ground truth of their network using plain human language.
Ask Questions, Get Evidence
Instead of writing complex KQL scripts, analysts can simply ask TensorGuard:
- “Are there any hidden forwarding rules in our Microsoft 365 tenant created within 24 hours of an unrecognized USB drive being inserted into a finance executive’s laptop?”
- “Review these 100 acquired laptops for any historical evidence of a dormant ransomware payload before we integrate them into our primary network.”
- “Did any unapproved remote access tools execute on our servers in the past 30 days to bypass our VPN?”
Crucially, in the high-stakes realm of corporate liability and M&A due diligence, assumptions are unacceptable. Every AI-generated claim is directly cited and hyperlinked to the raw, underlying binary and CSV data. You do not blindly trust a “black box” algorithm; your legal counsel and security leaders are handed cryptographically sound, legally defensible proof.
The Economic Imperative for the Enterprise
For the Chief Financial Officer, Corporate Development team, and Private Equity investors, the implications of the AI era are purely economic. The average cost of a U.S. data breach has eclipsed $10 million, driven almost entirely by dwell time—the length of time a threat actor remains undetected.
Relying on uncapped, hourly IR retainers for broad compromise assessments is financially unsustainable in a world where AI models commoditize zero-day exploits. TensorGuard completely disrupts the economics of Incident Response. By compressing a 20-week manual triage into ten minutes, TensorGuard delivers exponential ROI compared to manual DFIR engagements. It’s software, not consultants.
But the true ROI of automated forensics is found in breach avoidance. By utilizing TensorGuard to run continuous, automated compromise assessments across your fleet every 30 to 90 days, you mathematically cap your maximum potential dwell time. If a sweep uncovers a single dormant threat placed by an AI agent before data exfiltration occurs, the platform pays for itself exponentially.

The New Mandate for Enterprise Resilience
Project Glasswing is not a harbinger of the apocalypse; it is a blaring alarm. The revelations should permanently put an end to the illusion that reactive cybersecurity is sufficient. We are entering an epoch where the offense operates with the speed, precision, and relentless creativity of an advanced neural network.
To survive, organizations must abandon the hope that their perimeter is impenetrable. They must assume compromise, and build an architecture capable of instantly proving or disproving that assumption at any given moment.
You cannot out-patch an AI that generates zero-days on demand. You cannot rely solely on real-time sensors to catch an adversary that knows exactly how to render itself invisible. But you can shine a light into the darkest, most immutable corners of your network’s history.
And when an autonomous AI can generate a zero-day exploit in seconds, a ‘clean’ live-sensor dashboard is no longer a legally defensible proof of security. Ignorance of an entrenched threat is no longer an unfortunate reality of IT—it is corporate negligence.
The era of the amnesic enterprise is over. It is time to give your defenses a memory.