Table of Contents
In the high-stakes realm of corporate litigation, severe human resources disputes, and rigorous regulatory audits, technical suspicion is entirely irrelevant. The only currency that matters is cryptographically sound, legally defensible proof. When a whistleblower complaint is formally filed, a crucial executive submits their abrupt resignation, or a judge issues a legal hold, the corporate clock immediately starts ticking against the IT and Security departments.
In these critical scenarios, organizations require undeniable proof of user and system activity. However, relying on standard IT telemetry, routine system backups, or real-time security dashboards is a massive legal liability. These systems are ephemeral by design and legally insufficient for establishing a rigorous forensic chain of custody. To survive intense legal scrutiny and prevent the catastrophic spoliation of evidence, organizations must fundamentally change their approach to incident response by adopting a definitive “Collect Now, Analyze Later” methodology. TensorGuard empowers organizations to execute this strategy at enterprise scale, ensuring that evidence is preserved immutably and compliance is mathematically ensured.
The Degradation of Truth in Digital Forensics
The most profound challenge in legal hold data preservation is understanding that everyday, routine computer operation actively destroys digital evidence. According to the foundational forensic principle known as the Order of Volatility, data must be preserved from the most volatile to the least. Many IT professionals falsely assume that as long as a machine is powered on and functioning normally, the evidence on the hard drive remains intact. In reality, the Windows operating system is a highly dynamic environment that constantly overwrites its own history to preserve disk space and optimize performance.
The moment a policy violation or internal threat is suspected, the forensic integrity of the target endpoint begins to rapidly degrade with every passing second of regular use:
- Browser SQLite Databases: Web browser histories, which are vital for proving intent and tracing file acquisition, are stored in local SQLite databases utilizing Write-Ahead Logging (WAL). These are routinely overwritten and vacuumed by the browser as the user continues to surf the web.
- Windows Event Logs (
.evtx): Standard event logs, such as the Security and Application logs, have fixed maximum size limits. In a busy enterprise environment, critical authentication and process creation logs are routinely overwritten in a matter of days, erasing the historical record of an intrusion. - The Master File Table (
$MFT): When an insider threat deletes a staged archive of stolen intellectual property to cover their tracks, the$MFTsimply marks that record as “inactive.” However, if the system continues to operate, the OS will eventually reallocate that space to a new file, permanently destroying the metadata required to prove the theft ever occurred.
To protect the organization, security teams cannot wait days or weeks for external counsel to authorize an expensive forensic investigation. The ground truth must be captured immediately.

The .spade Package: Proactive Data Preservation
TensorGuard solves the degradation of truth by aggressively decoupling the act of collection from the act of analysis. Traditionally, preserving an endpoint required physically seizing the laptop, removing the hard drive, and utilizing hardware write-blockers to create a bit-for-bit physical image—a process that takes hours, alerts the employee to the investigation, and severely disrupts business continuity.
By utilizing the TensorGuard Forensic Collector, internal security teams can perform a remote forensic collection instantly, without alerting the user or disrupting their daily workflow. The collector quietly and rapidly compiles an immutable, heavily encrypted .spade collection package. This package serves as a comprehensive, point-in-time snapshot of the device’s deepest forensic artifacts—locking the $MFT, ShellBags, AmCache, and Event Logs in cryptographic amber before the evidence can be deliberately or accidentally destroyed.
You do not need to know exactly what you are looking for at the moment of collection. You merely secure the state of the machine. The encrypted .spade package can be safely archived in cold storage for months or years to satisfy data retention policies or legal hold requirements.
Automating the Chain of Custody (Alpha 7 Innovations)

In any legal proceeding, digital evidence is immediately challenged by opposing counsel. If an organization cannot unequivocally prove exactly who collected the data, how it was encrypted, where it was stored, and who has accessed it since, the findings can be successfully challenged and ruled inadmissible.
With the release of TensorGuard Alpha 7, we have completely automated the logistical and cryptographic overhead required to maintain absolute legal defensibility.
FIPS-Aligned Architecture and Defensibility
- FIPS-Aligned Collection Defaults: To meet the rigorous standards required by federal agencies and heavily regulated industries, TensorGuard
.spadecollection packages now default to FIPS standards. The collection process utilizes the heavily auditedaws-lccryptographic library, compiled specifically for FIPS usage, to ensure the encryption and integrity hashing of the collected artifacts. (Note: While our underlying libraries are audited and we utilize FIPS standards, TensorGuard itself is currently pending external FIPS validation). - Mandatory Attestation Statements: The manual collection interface now strictly requires digital attestation statements from the collecting officer, fulfilling critical legal and HR procedural requirements directly at the point of collection, confirming the authorization and scope of the acquisition.
- Chain of Custody Exports (v1): Full custodial reports are automatically generated as PDF exports for all collected artifacts. These reports provide a legally defensible audit log detailing exactly who executed the collection, the precise timestamp of acquisition, and an immutable log of every TensorGuard user who has accessed or viewed the data since it was uploaded to the platform.
Future-Proofing Your Organization
The financial and reputational devastation of a data breach or catastrophic insider theft is compounding exponentially every single year. As the frequency and sophistication of these attacks reach unprecedented highs, delaying forensic data preservation is no longer just an operational oversight—it is a massive, inexcusable financial liability.
The upfront cost of proactively capturing an immutable forensic snapshot is absolutely minuscule compared to the catastrophic alternative. You are effectively paying fractions of a penny on the dollar to secure your ground truth, whereas failing to collect this data guarantees exorbitant legal settlements, regulatory fines, and blind, panicked emergency IR retainers when the evidence is inevitably overwritten.
If your organization is not aggressively collecting forensic data today, you are actively choosing to be legally defenseless tomorrow.
By embracing the “Collect Now, Analyze Later” philosophy, organizations gain total strategic flexibility. When a high-risk executive departs, you can proactively capture a .spade package during their off-boarding and store it securely. You do not need to pay for forensic analysis immediately. However, if a competitor suddenly launches a suspiciously similar product eight months later, you are fully prepared.
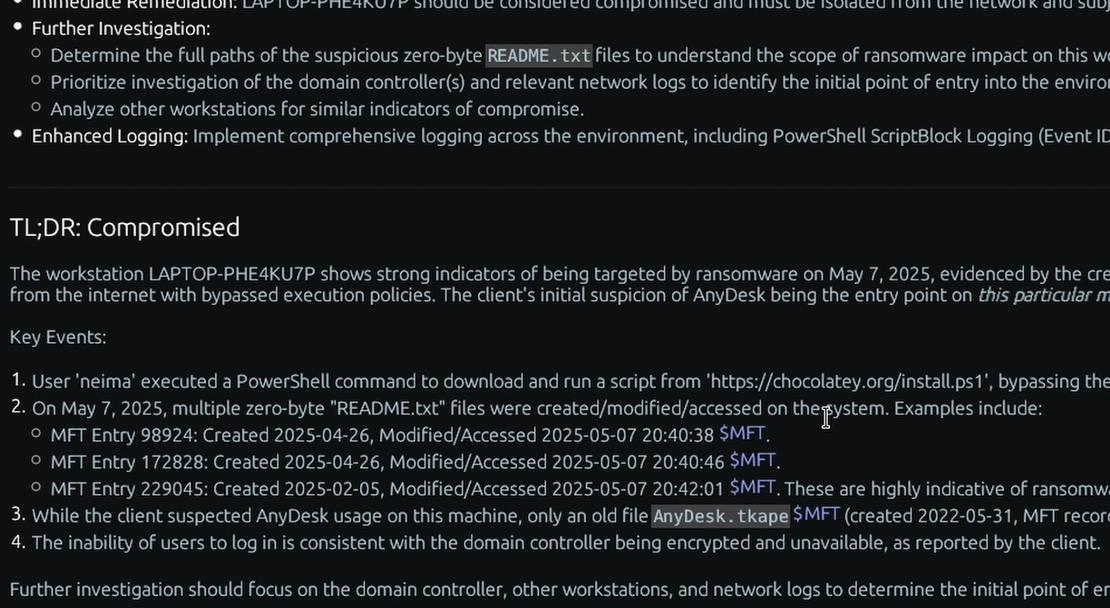
You simply upload the preserved .spade package into the TensorGuard Console, ask the Evie 2.0 AI to search for indicators of intellectual property theft, and receive an airtight, legally defensible executive report in under ten minutes. Proactive, FIPS-aligned digital forensics is the ultimate corporate insurance policy.