Table of Contents
It is 4:00 PM on a Friday. Human Resources urgently notifies the IT Director that a disgruntled mid-level engineer—someone with unrestricted access to your entire client database—is being terminated.
The employee’s accounts are locked, but Legal and HR ask a single, sweat-inducing question: “Are we sure they didn’t take our proprietary data before we pulled their access?”
Under the traditional security paradigm, answering that question is an agonizing ordeal. Your Endpoint Detection and Response (EDR) platform is completely silent. The employee didn’t download malware; they simply used their legitimate credentials to move files—a behavior real-time tools inherently ignore to prevent false positives.
To definitively prove whether data was exfiltrated, IT is forced into a corner. You must physically confiscate the laptop, lock it in a drawer, and engage a third-party digital forensics firm on an emergency retainer. You wait weeks for a consultant charging $700 an hour to manually parse the Master File Table ($MFT) and AmCache. By the time the invoice arrives and the answer is delivered, your client list has already been handed to a competitor.
Caught between the exorbitant cost of a full forensic autopsy and the paralyzing delay of a third-party retainer, most organizations default to a terrifying alternative: they simply wipe the hard drive for the next new hire, and blindly hope their intellectual property didn’t just walk out the front door.
This five-figure, multi-week nightmare plays out in corporate IT departments and Managed Service Providers (MSPs) every single week. And it is merely a symptom of a much larger, systemic illness.
The Telemetry Trap
Walk into any modern IT department today, and you will find a team drowning in telemetry but starving for truth.
The cybersecurity industry is currently trapped in a paradox: our defensive tools have never been more advanced, yet the humans tasked with running them have never been more exhausted. The volume, velocity, and sophistication of cyberattacks are scaling exponentially, generating massive alert backlogs that bury the actual threats in noise.
This isn’t just a crisis for elite corporate Security Operations Centers (SOCs). The true frontline of the cyber war is manned by internal IT departments and MSPs—lean teams who are increasingly expected to act as world-class threat hunters while simultaneously keeping the daily operational lights on.
The Gatekeepers of Ground Truth
Historically, proactive threat hunting and deep-dive incident response operated like an exclusive club with an exorbitant cover charge.
To interrogate a network for specific malicious behaviors, an IT professional couldn’t just ask a question; they had to translate their suspicion into complex query languages. To search a SIEM, you had to master Splunk Search Processing Language (SPL) or Microsoft’s Kusto Query Language (KQL). To scan a fleet for malware attributes, you had to write flawless YARA rules. If you needed to unearth the deepest artifacts of the Windows operating system, you were forced to utilize disparate command-line utilities to extract and format raw binary data.
These highly specialized syntaxes act as gatekeepers. Expecting a generalized IT team—or an over-extended MSP helpdesk managing the infrastructure of fifty different corporate tenants—to simultaneously master these languages while handling daily ticket triage is a mathematical and psychological impossibility.
The result? Deep, evidence-based threat hunting remains locked behind a language barrier, practiced only by a handful of senior personnel or highly paid external consultants. Vast segments of the digital fleet are left completely unexamined.
To break this cycle, we have to fundamentally rethink who is “allowed” to do digital forensics. We have to democratize the dark art of DFIR.
Intelligence, Not Just Data: The Evie 2.0 Engine
TensorGuard was built on a simple, radical philosophy: You shouldn’t need a PhD in computer science to know if your network is compromised.
With the release of our Evie 2.0 Intelligence Engine, we have successfully bridged the gap between deep forensic science and operational accessibility. TensorGuard automates the complex, tedious phases of data collection and artifact parsing. Instead of dumping millions of rows of raw data onto an IT administrator’s desk, Evie 2.0 processes this raw data chaos into clear, actionable intelligence.
Operationalizing Forensics for the Frontline
- For the MSP (Margin Expansion): Instantly validate low-fidelity EDR alerts across your entire client base without escalating to a specialized, third-party IR firm. You maintain control of the client relationship, accelerate resolution times, and keep the revenue in-house.
- Context Over Clutter: Instead of requiring a technician to decipher a cryptic registry offset, TensorGuard groups complex data into simple, intuitive “Indicators.” It plainly states: “Program X was executed,” or “User Y copied File Z to a SanDisk USB.”
- Evidence-Linked Certainty: Evie 2.0 isn’t a black box. Every AI-generated summary and timeline event is directly linked to the underlying raw forensic artifact. Junior technicians and auditors can instantly verify the AI’s logic, bringing absolute, legally defensible certainty to the investigation.

Conversational Security: Plain-Language Threat Hunting
TensorGuard’s most transformative capability is the introduction of plain-language queries directly into the threat hunting workflow.
Your IT staff and MSP analysts are no longer constrained by the shallow, real-time telemetry of traditional tools; they can now directly interrogate the deep, historical forensic ground truth of an endpoint using natural human language. The Evie 2.0 engine translates the intent, queries the fleet-wide forensic database, and returns legally defensible, artifact-backed answers in minutes.
Ask Questions, Get Evidence
An IT administrator or MSP technician can immediately launch sophisticated, fleet-wide investigations simply by typing:
- “Have any unapproved remote access tools—like personal versions of AnyDesk or TeamViewer—been executed on our servers in the past 30 days to bypass our official VPN?”
- “Show me every instance this week where a USB storage drive was connected to a workstation in the finance department, and list exactly which files were accessed or compressed right before the drive was inserted.”
- “Review these 50 newly onboarded laptops for any historical evidence of a previous data breach, dormant ransomware staging, or unauthorized administrative activity before we connect them to our primary network.”
The 4:15 PM Resolution
Armed with conversational security, let us return to our terrified IT Director facing the Friday afternoon offboarding crisis.
With TensorGuard, that five-figure, multi-week nightmare becomes a ten-minute task.
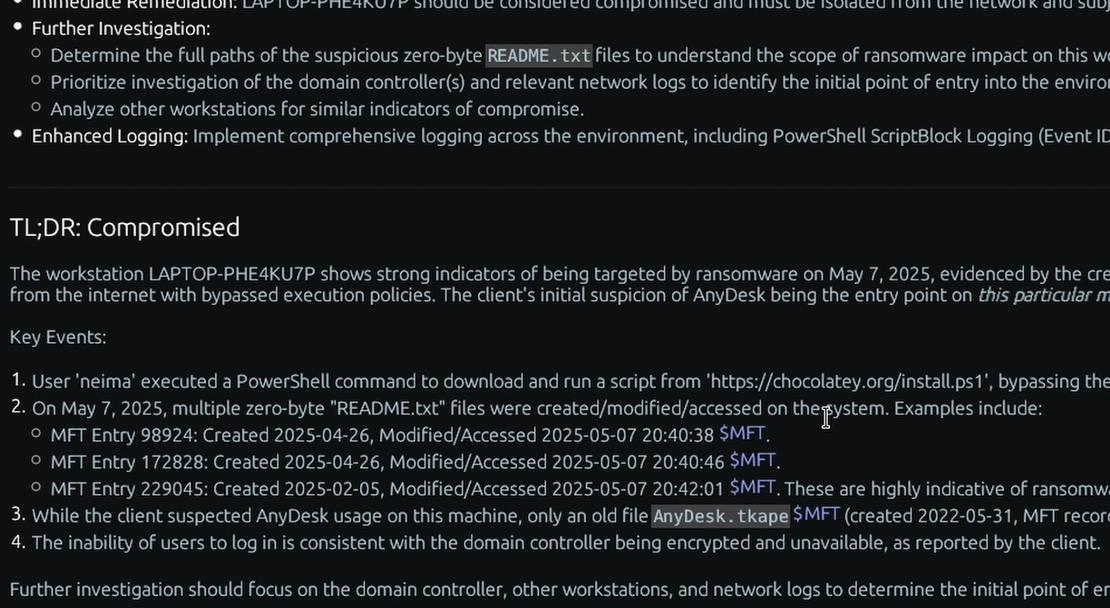
Without ever leaving their desk, an IT admin or MSP analyst remotely takes a lightweight forensic collection from the terminated employee’s machine. Once the historical data is ingested, the analyst simply asks the Evie 2.0 engine: “The user of this device was recently terminated. Did they take any files on the way out?”
By 4:15 PM, the technician hands HR and Legal a cryptographically sound, artifact-backed executive summary. The AI has automatically correlated the file staging in the $MFT with the precise moment a USB drive was inserted, linking every claim directly to the underlying binary proof.
You don’t just suspect it; you prove it. For a lean IT team or an MSP, achieving this level of instant, correlated visibility without writing a single line of code isn’t just an operational upgrade—it’s historically unthinkable.
The Ripple Effect of Ground Truth
The implications of that 4:15 PM resolution extend far beyond the IT department.
Consider the boardroom. When a suspected incident occurs, executives inevitably ask a binary question: “Are we compromised?” In a legacy environment, answering that plain-English question requires a multi-day translation effort. The business query is translated into an IT ticket, translated into a complex query language by an external consultant, and finally back into a boardroom presentation. By the time the executives receive their answer, the adversary has won, and the CFO is left staring at a blank-check invoice for an hourly Incident Response retainer.
Paying elite forensic rates to manually parse file systems is the financial equivalent of hiring a neurosurgeon to take a patient’s temperature.

Because TensorGuard operates in natural human language, it severs this dependency. The answers generated by your staff are already formatted in the dialect of business risk—delivered in minutes, completely bypassing the unpredictable economics of external retainers.
But perhaps the most profound impact of democratizing digital forensics isn’t found on the balance sheet; it is found in the psychological reality of the modern IT professional.
Today’s helpdesks often function less like investigative units and more like digital assembly lines. Junior staff sit at the bottom of a waterfall of alerts, acting as “human routers” who escalate critical anomalies simply because they lack the arcane syntax required to dig deeper. Analysts do not quit because the work is too intellectually rigorous; they quit because the structural friction of their tooling renders the job profoundly unfulfilling.
By abstracting the complexity of forensics, Evie 2.0 hands your staff the agency to actually solve the puzzle. When you empower your baseline team to execute the deeply satisfying, high-value work previously reserved for elite threat hunters, you transform an exhausted triage desk into a proactive intelligence unit.
You don’t just secure the network. You rescue the people tasked with defending it.
The Ultimate Force Multiplier
By democratizing DFIR through automated threat hunting, TensorGuard empowers your existing IT team or MSP partners to perform at the level of elite forensic consultants. Reduce organizational risk, cap financial liability, and retain top talent—without expanding your headcount.