Endpoint Detection and Response (EDR) platforms are the undisputed cornerstones of the modern enterprise security stack.
Industry-leading solutions like CrowdStrike and SentinelOne are exceptionally engineered for live, real-time defense. They continuously monitor active memory, hook critical system processes, and isolate hosts at the first sign of an active intrusion.
Your Security Operations Center (SOC) relies on these tools daily to terminate malicious execution the exact millisecond it triggers a behavioral heuristic. They do an incredible job securing the live environment.
However, enterprise security leaders frequently fall into the dangerous trap of believing that a “green dashboard” equates to total, uncompromised endpoint visibility.
A Security Camera Analogy
When evaluating EDR vs DFIR (Digital Forensics and Incident Response), it is vital to understand a fundamental architectural reality:
EDR operates much like a security guard watching a live camera feed. It is incredibly effective at stopping a break-in currently in progress, but it possesses a severe blind spot.
A live security camera cannot see what successfully evades its live monitoring, and it cannot see what occurred before it was installed.
This leaves security teams with one vital, often unanswered question:
Were we already compromised and just don’t know it?
To achieve true, impenetrable security and eliminate these EDR blind spots, the live-feed capabilities of traditional endpoint protection must be fundamentally augmented by the immutable, historical ground truth of automated digital forensics.
The Limitations of Live Telemetry
Security Operations Center (SOC) teams are consistently inundated with alerts, but they often lack the historical context to determine if an alert is a false positive or the vanguard of a critical breach. In a perfect world, live telemetry would catch every intrusion.
In reality, advanced adversaries—including state-sponsored Advanced Persistent Threats (APTs) and highly privileged malicious insiders—intimately understand exactly how EDR agents function and how to elegantly bypass them.
The most critical limitations of EDR stem from its reliance on evaluating the behavior of active processes. Because continuous, deep disk parsing would incur unacceptable computational overhead on a live endpoint and degrade system performance, EDR platforms inherently ignore the deepest, most authoritative forensic databases of the Windows operating system.
CrowdStrike and SentinelOne Evasion
Modern adversaries rarely drop noisy, easily recognizable custom malware payloads (like unsigned .exe files) onto a disk where EDR can simply signature them. Instead, they operate in the shadows of legitimate administrative workflows by employing “Living-off-the-Land” (LotL) and fileless malware techniques.
Attackers hijack native, trusted Windows operating system binaries and highly privileged administrative tools like PowerShell, Windows Management Instrumentation (WMI), or certutil.exe. Because these tools are cryptographically signed by Microsoft and legitimately required for daily enterprise IT operations, EDR platforms are fundamentally hesitant to block them outright. If an EDR aggressively blocks a legitimate WMI process, it risks taking down critical production servers.
The security platform is forced to evaluate the context of the execution. This hesitancy allows threat actors to suppress live alerts, blend their actions into the background noise of standard administrative traffic, and move laterally entirely undetected, consistently achieving CrowdStrike evasion.
Furthermore, EDR provides near-zero visibility into historical compromises.
Consider an acquisition scenario (M&A due diligence), or simply rolling out a new EDR agent to legacy infrastructure: if a threat actor compromised a server and established a dormant backdoor months before the new EDR agent was deployed, the newly deployed agent will likely interpret the attacker’s pre-established persistence mechanisms as baseline, standard operating procedure. This severe lack of historical memory leaves vast segments of your enterprise infrastructure unexamined and vulnerable.
TensorGuard: Giving Your EDR a Memory

TensorGuard does not replace your EDR, your CrowdStrike or your SentinelOne; it acts as its essential “time machine” and proactive complement.
TensorGuard was engineered to bridge this exact operational gap. By aggressively decoupling forensic collection from real-time analysis, our platform operates without the computational constraints of a live agent. TensorGuard quietly queries the immutable OS artifacts that EDR leaves behind, completely restoring historical visibility and capturing the complete lifecycle of an attack.
Validating Low-Fidelity Alerts
When your EDR throws a low-fidelity, ambiguous alert regarding suspicious activity—such as an unusual PowerShell script execution—your SOC no longer needs to guess. TensorGuard provides the historical ground truth, empowering your team to instantly pivot from a live alert into a deep, fleet-wide forensic timeline.
Exposing the Invisible: Integrating Deep Forensic Artifacts
When an EDR sensor flags an unusual activity, analysts can utilize TensorGuard to instantly pull the device’s comprehensive forensic history via a lightweight, read-only .spade collection package. Our Evie 2.0 Intelligence Engine parses the data in parallel, automatically interrogating the foundational artifacts that real-time tools ignore:
Restoring the Historical Ground Truth
ShimCache: Did a malicious binary execute on this system weeks ago and actively self-delete to evade EDR? TheShimCacheretains the execution record, complete with file paths and precise timestamps, establishing definitive proof of execution even after advanced anti-forensic wiping.AmCache: By parsing theAmCache, TensorGuard automatically correlates execution events with SHA1 hashes. This exposes the usage of portable hacking tools executed from unmonitored, external USB drives that live sensors missed entirely.System Resource Usage Monitor (SRUM): Is a supposedly benign system process (likesvchost.exe) occasionally beaconing to a Command and Control (C2) server?SRUMprovides 60 days of rolling historical data detailing exactly which application utilized network bytes, retroactively tracking data exfiltration and completely bypassing the need for expensive live Packet Capture (PCAP).PowerShell History: Are attackers utilizing authorized administrative tools to move laterally? TensorGuard extracts the raw PS ReadLine history, providing a literal, sequential script of the attacker’s activities. This reveals the exact, obfuscated scripts and cmdlets typed by the adversary, cutting through live-memory obfuscation.
Democratizing DFIR with Plain Language Threat Hunting
Traditionally, augmenting EDR with deep historical forensics required escalating the ticket to a highly specialized, expensive DFIR consultant fluent in complex command-line utilities and proprietary query languages like KQL or SPL. Expecting an entire SOC of Tier 1 analysts to manually extract registry hives during a fast-moving incident is mathematically impossible. This created a massive operational bottleneck, extending adversary dwell times.
TensorGuard democratizes this elite capability at fleet-wide scale. Powered by the Evie 2.0 Intelligence Engine, we empower your internal Tier 1 and Tier 2 security teams to validate EDR alerts and proactively hunt for LotL attacks by asking specific, highly targeted questions about your environment in plain human language.
Ask Questions, Get Evidence
Analysts can immediately launch sophisticated, fleet-wide threat hunts simply by typing:
- “Please perform a compromise assessment for these devices.”
- “Which applications generated the most network traffic last month across our sales team’s laptops?”
- “Carry out a thorough insider threat assessment for these devices, we just had an incident with a terminated employee.”
- “Show me all devices where a USB drive was connected in the last 72 hours, and tell me what files were accessed.”
- “Has the tool
mimikatz.exeor other common hacking tools ever been run on these domain controllers?”
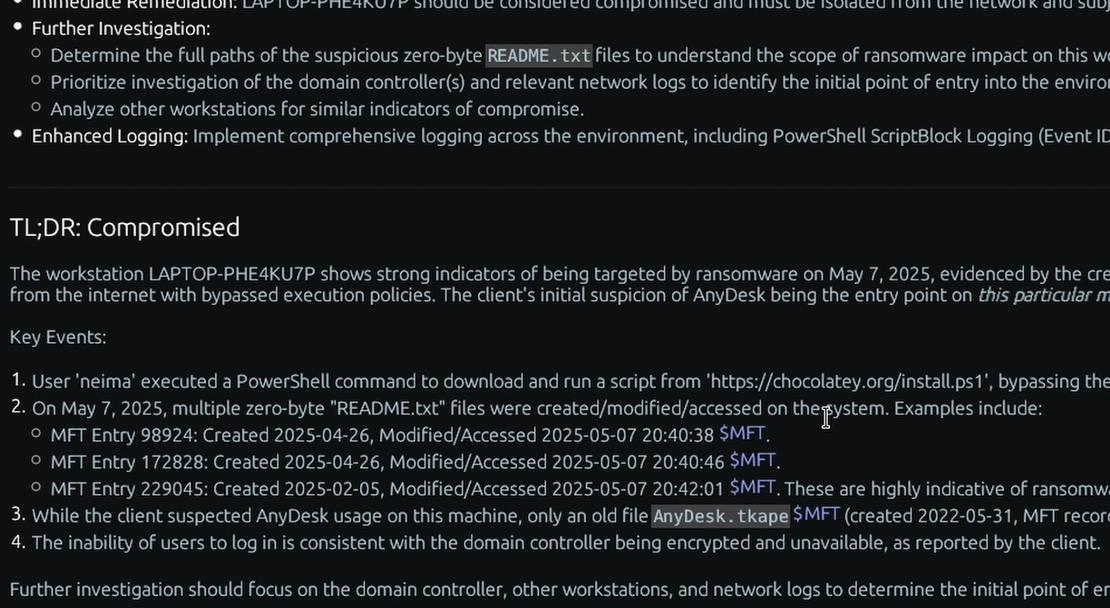
Within minutes, TensorGuard translates the intent, queries the fleet-wide forensic database, and returns structured intelligence. Reports are not just massive, unreadable data dumps. They begin with plain-English Executive Summaries that instantly answer the core question—was this system compromised, yes or no?—before automatically prioritizing the most critical findings for your analysts.
Crucially, every single AI-generated claim is directly cited and hyperlinked to the underlying raw forensic hex and CSV data. Compiling this level of artifact-linked reporting is incredibly time-intensive for a human consultant to generate manually from scratch, but it is exceptionally time-efficient for a human to validate. Your analysts are never asked to blindly trust a “black box” algorithm; they are provided with verifiable, cryptographically sound proof they can instantly audit themselves.
The Unified Endpoint Strategy: A Complete Security Posture
Security is not a single product; it is an integrated architecture. Relying exclusively on real-time sensors is a dangerous gamble against sophisticated modern threat actors. True enterprise resilience requires balancing the live-action mitigation of CrowdStrike and SentinelOne with the deep, irrefutable historical analysis of a modern Digital Forensics and Incident Response (DFIR) platform.
Proactive Resilience
By fusing the reactive, live-blocking capabilities of EDR with the deep, proactive, and historical visibility of TensorGuard, you close the operational blind spot. You gain a powerful, evidence-based view into the past, present, and future security of your endpoints.
By integrating automated compromise assessments into your weekly EDR workflows, you transition your SOC from a state of reactive firefighting to proactive, evidence-backed threat hunting. You transition from hoping you are secure to proving it with verifiable, artifact-linked certainty across the past, present, and future of your endpoints.
| Live Security Tooling (EDR) | TensorGuard Platform | |
|---|---|---|
| Visibility | Real-time and forward-looking: Inherently blind to activity that occurred before the agent was installed or when it was evaded. | Historical forensic ground truth: Analyzes years of on-device artifacts, looking backward to uncover the complete history. |
| Core Question | “What is actively happening in our environment right now?” | “Were we already compromised and just don’t know it?” |
| Operational Paradigm | Reactive active-defense: Relies on continuous monitoring and alert-driven responses to known malicious behaviors. | Proactive automated forensics: Enables scheduled, fleet-wide compromise sweeps to continuously assess security posture. |
| Evidence Depth | Behavioral telemetry: Highly effective for rapid endpoint isolation and tracking active process trees. | Defensible forensic artifacts: Provides direct citations to raw underlying data (e.g., $MFT, AmCache, ShellBags). |
| Primary Strengths | Stopping active malware & exploits: Essential for blocking ongoing attacks and maintaining network/process defense. | Exposing dormant threats & insiders.: Unrivaled in uncovering historical data theft, policy violations, and prior breaches. |
| Analysis Speed | Instant queue generation: Generates alerts instantly, but subsequent manual DFIR investigations often take weeks. | Answers in minutes: Synthesizes raw data from thousands of endpoints into executive narratives, typically in under 10 minutes. |